BENGALURU — Somewhere in India this IPL season, a cricket fan stood at a stadium gate, paper ticket in hand, QR code glowing on their phone screen, only to be turned away. The seat they had paid for never existed. The website that sold it to them had vanished. The money was gone.
They were not alone.
Cybersecurity firm CloudSEK has pulled back the curtain on what may be the most sophisticated cricket-themed fraud operation ever documented in India — a sprawling, industrialised scam ecosystem that weaponised fan emotion, exploited the urgency of sold-out matches, and quietly delivered malware to thousands of devices under the cover of a free live stream.
Registration Begins for FutureCrime Summit 2026, India’s Largest Cybercrime Conference
The numbers are staggering. Researchers identified over 600 fraudulent domains selling fake IPL tickets and more than 400 fake streaming websites — many of them not just stealing money, but actively serving as malware delivery systems capable of draining bank accounts, browser sessions, and even cryptocurrency wallets.
The Ticket That Felt Real Until It Wasn’t
The scam begins where most things do today — a scroll.
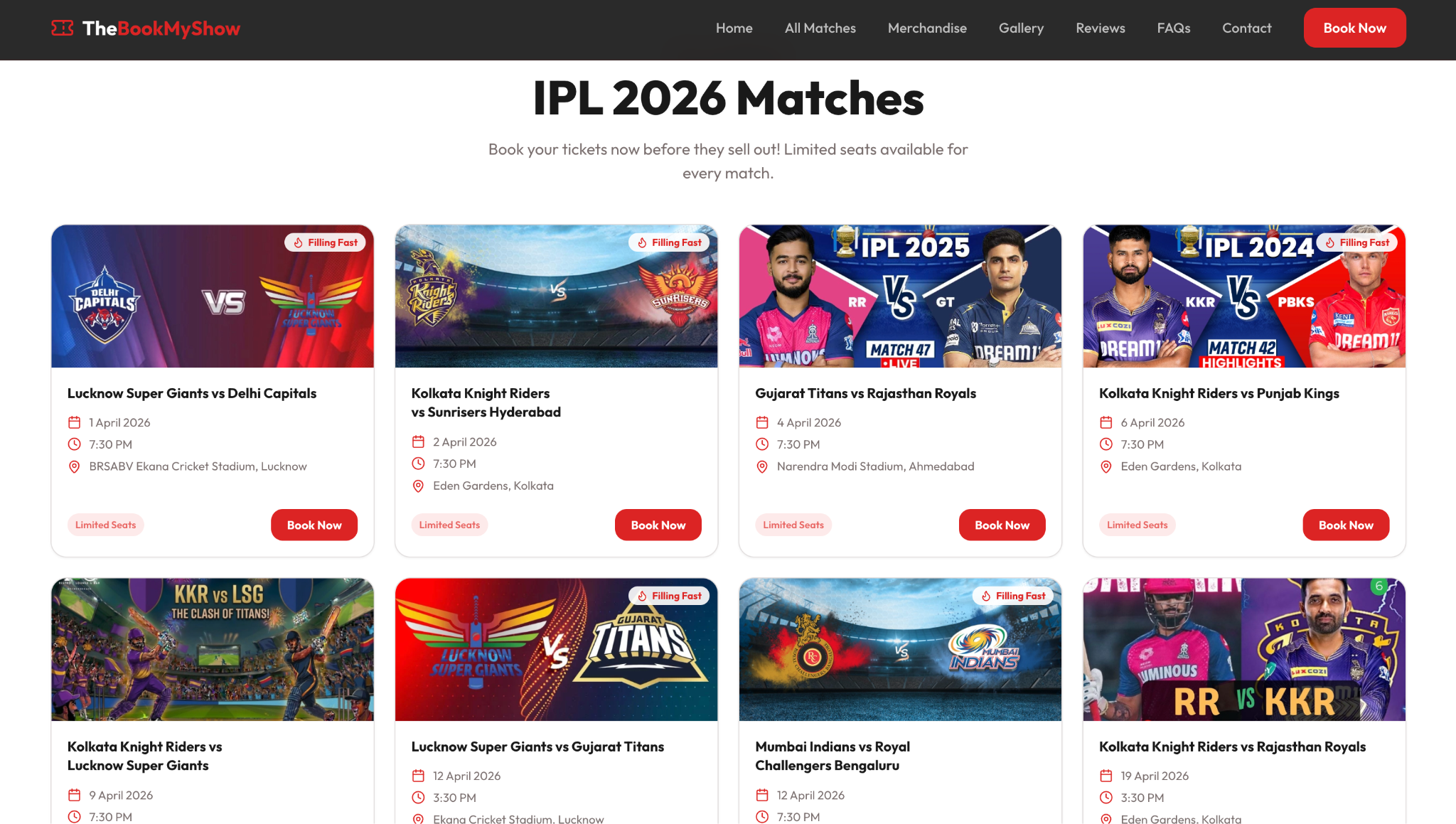
A Reel. A Facebook post. A Telegram forward promising last-minute pavilion seats for the big rivalry match. The website it leads to is polished. Team logos gleam. A countdown timer ticks. A banner warns that only three seats remain in your preferred stand. The familiar colour palette of a trusted ticketing brand wraps the entire page like a costume.
The fan picks their seat. Fills in their details. Pays via UPI or card. And within minutes, a PDF lands in their inbox — complete with seat numbers, booking references, professional branding, and a scannable QR code.
At the stadium gate, the QR code fails. Security doesn’t budge. The match goes on without them.
What CloudSEK’s researchers found next, however, is what separates this from your average phishing page. They gained access to the admin backend of one of these fake ticketing operations — and what they found inside looked less like a scam and more like a startup.
The panel was built for scale. It tracked bookings in real time. It stored victim names, phone numbers, and email IDs. It let operators manually verify incoming UPI payments before dispatching fake tickets — a deliberate step to reduce the risk of sending PDFs to people who hadn’t actually paid. It had match management modules, price controls, and a one-click system to generate and email convincing fake tickets on demand.
And then there was this detail: Meta Pixel integration.
The fraudsters were running their scam like a performance-marketing campaign. They tracked which ads brought in the most victims, which creatives converted best, which match fixtures drove the highest purchase intent. They were A/B testing their fraud.
“The fake ticketing backend shows how industrialised these scams have become,” said Sourajeet Majumder, Security Researcher at CloudSEK. “Operators are not only selling fake tickets. They are tracking conversions, adjusting prices, verifying payments and collecting victim data that can be reused or sold for future scams.”
The Stream That Stole Everything
If the ticketing fraud preyed on those trying to get into the stadium, the streaming fraud preyed on everyone else — the hundreds of millions watching from home, offices, and phones.
FCRF Academy Launches Premier Anti-Money Laundering Certification Program
Free IPL streaming has always been the holy grail of Indian cricket fandom. Every season, a significant portion of fans goes hunting for it. Cybercriminals know this hunt better than anyone.
CloudSEK found over 400 fake streaming sites optimised specifically for high-intent searches — “IPL 2026 free live stream,” “watch IPL online free,” “DC vs RCB live stream” — terms that spike in search volume minutes before a big match kicks off. Many of these sites looked convincingly real: match listings, team names, streaming buttons, quality selectors, and navigation menus that implied a fully functional platform beneath.
But the moment a visitor clicked play, the real operation began.
Researchers documented a layered chain of pop-unders, forced redirects, and browser-detection scripts that quietly identified a user’s operating system before routing them to a device-specific trap. For macOS users in particular, the experience was chilling.
The site would redirect them to a page impersonating a GitHub installer or an Apple macOS security update. A prompt would instruct the user to open Terminal and paste a command. To a non-technical user, it looked like a necessary step to enable the stream. What it actually did was retrieve and execute a malicious payload.
That payload had a name: SHub Stealer.
SHub Stealer: The Malware Behind the Free Match
SHub Stealer is a macOS infostealer — a category of malware designed to operate quietly in the background while systematically looting everything of value from an infected machine. CloudSEK’s analysis of its capabilities reads like a worst-case scenario for any device owner.
The malware harvests macOS login passwords, browser passwords and cookies, Chrome master password data, Telegram Desktop sessions, Apple Keychain data, iCloud credentials, Safari cookies, history and autofill data, Apple Notes databases, and files from the Desktop and Documents folders.
For cryptocurrency holders, the threat is existential. SHub Stealer targets data from over 100 crypto wallet browser extensions and desktop wallets including Exodus, Atomic, Electrum, Coinomi, Ledger Live, and Trezor Suite. In cases where popular wallet applications were installed, the malware went further — modifying application files to capture wallet seed phrases, the master keys that grant irreversible access to a victim’s funds.
To ensure it isn’t evicted after the initial theft, the malware establishes persistence through a fake Google Update application and a background LaunchAgent that continues running silently on the device.
“What appears to be a free match stream can become a full device compromise,” Majumder said. “The victim thinks they are watching cricket. In the background, their passwords, browser sessions, files and crypto wallet data may already be leaving the system.”
Why IPL, and Why Now
The logic of targeting IPL is almost uncomfortably simple. Few events in India combine the sheer audience scale of the tournament with the emotional volatility of its fanbase and the compressed, high-pressure transactional window it creates. Tickets sell out fast. Matches happen at fixed times. FOMO is not a marketing buzzword here — it is a genuine psychological state affecting millions of people simultaneously.
Fraudsters understand this architecture intimately. CloudSEK’s report notes that the fraud infrastructure does not materialise overnight. Domains are registered weeks in advance. Telegram channels are seeded with fake testimonials. Social media pages are built up with manufactured credibility. Paid ads are prepared and held in reserve. The campaigns fire when the match calendar heats up — intensifying around high-profile rivalries, playoffs, and the final.
By the time the trophy has been lifted and the confetti has settled, most of the domains are already abandoned — dormant until the next major cricket event gives them reason to wake up again.
What You Should Do Before the Next Match
CloudSEK’s guidance is direct: buy tickets only through the BCCI website or its officially authorised partners. Any ticket offer surfacing through social media, a messaging app, or an unfamiliar website — no matter how convincing the branding — should be treated as suspect.
For streaming, only use authorised broadcast platforms. Any site offering a free live stream and asking you to click a button, download a file, or run a command on your device is not giving you cricket. It is taking something from you.
The stadium gate doesn’t lie. The fake ticket always fails there.
The malware, unfortunately, is far less visible.


