A massive Distributed Denial of Service (DDoS) attack has been reported, generating over 2.45 billion malicious requests within just five hours against a large user-generated content platform. The incident highlights a rapidly evolving cyber threat landscape where attackers are increasingly using distributed, low-intensity traffic to bypass conventional security systems.
Low-Volume Traffic Used to Evade Detection
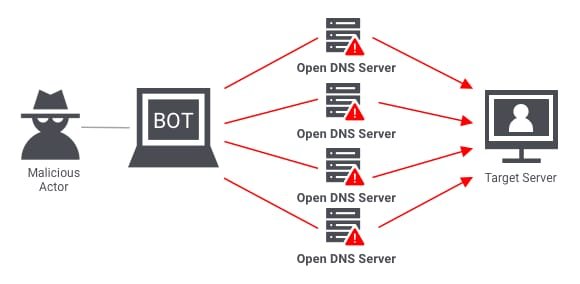
According to cybersecurity researchers, the attack was not a typical high-volume traffic flood. Instead, it was carefully engineered using a highly distributed botnet consisting of approximately 1.2 million unique IP addresses. This allowed the attackers to avoid triggering traditional rate-limiting defenses that rely on identifying abnormal traffic spikes from individual sources.
FCRF Academy Launches Premier Anti-Money Laundering Certification Program
At its peak, the attack reached around 205,000 requests per second, while maintaining an average of nearly 136,000 requests per second over the duration of the campaign. Despite the massive scale, each individual IP sent extremely low traffic volumes, roughly one request every nine seconds, making detection significantly more difficult.
Security analysts observed that the attackers deliberately structured the traffic into wave-like patterns, with intermittent pauses designed to reset rate-limit counters. During these pauses, the botnet rotated IP addresses, modified request headers, and altered user-agent strings to maintain continuous pressure on the target system without raising immediate alarms.
Global Botnet Blended With Cloud Traffic
The infrastructure behind the attack spanned more than 16,000 autonomous systems, indicating a highly fragmented and globally distributed network. Interestingly, no single ASN contributed more than 3% of the total traffic, ensuring that blocking individual networks would have minimal impact on the overall attack.
Investigators also found that the attackers used a combination of anonymization-friendly infrastructure and mainstream cloud providers. Traffic was routed through services associated with major platforms such as AWS, Cloudflare, and Google, alongside lesser-known privacy-focused hosting networks. This blending of malicious and legitimate traffic sources made filtering significantly more challenging for defenders.
While the attack demonstrated strong coordination, experts noted that the attackers did not employ advanced browser emulation or sophisticated client-side automation. Instead, they relied on basic request manipulation techniques, including rotating headers, cookies, and URL parameters to mimic legitimate traffic patterns.
Behavioral Detection
Cybersecurity firm DataDome’s Galileo threat research team played a key role in detecting and mitigating the attack in real time. Analysts explained that traditional static rate-limiting systems were ineffective against such distributed traffic patterns, requiring a shift toward behavioral detection methods.
The mitigation strategy involved analyzing long-term traffic behavior, identifying inconsistencies in session patterns, and applying reputation-based IP filtering. By correlating anomalies across multiple layers of network activity, defenders were able to distinguish between legitimate user traffic and coordinated botnet activity.
Security experts emphasized that this incident reflects a broader shift in DDoS tactics, where attackers prioritize stealth and distribution over raw traffic volume. Instead of overwhelming systems through brute force, modern attacks are designed to blend into normal traffic flows while gradually degrading system performance.