For many iPhone users, the loss of a device is not just the loss of a phone. It is the loss of photographs, contacts, bank-linked apps, personal messages, documents and access to a tightly connected digital life. That anxiety is now being exploited in a new phishing campaign identified by the National Cybercrime Threat Analytics Unit (NCTAU) of I4C.
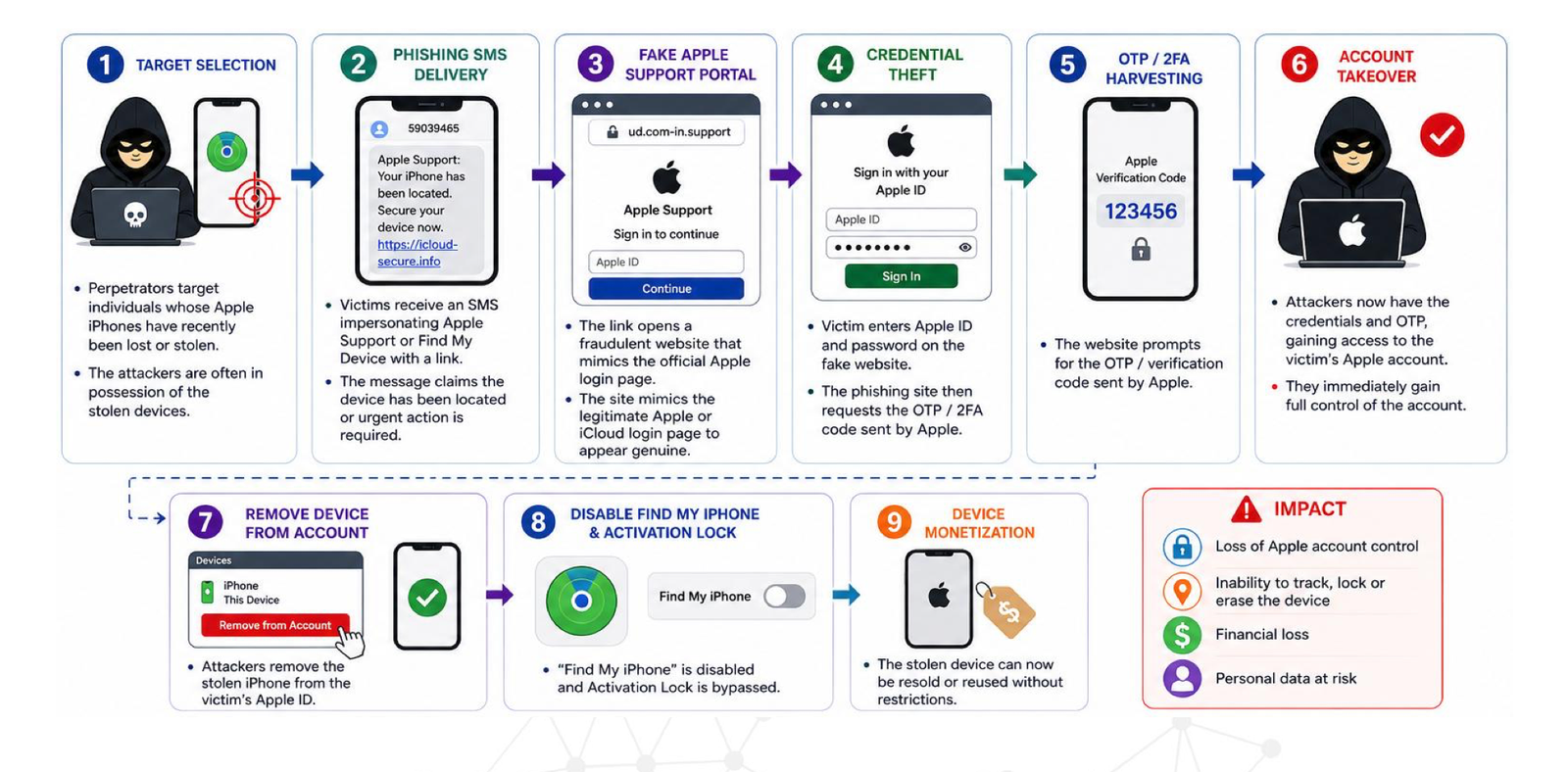
According to the advisory material, the campaign targets Apple iPhone users whose devices have been lost or stolen and are believed to be in the physical possession of perpetrators. The attackers then impersonate Apple Support or services linked to “Find My iPhone,” sending fraudulent SMS messages that appear to offer help in locating, securing or erasing the missing device.
The messages are designed to look urgent and familiar. Victims may be told that their lost device has been temporarily switched off, or that immediate action is needed to erase contacts, media or other sensitive data. The apparent purpose is reassurance. The actual purpose, investigators warn, is credential theft.
Registration Begins for FutureCrime Summit 2026, India’s Largest Cybercrime Conference
Once the victim clicks the link, they are taken to a counterfeit Apple Support or iCloud login page. There, they are asked to enter their Apple ID credentials and, in many cases, the one-time password or two-factor authentication code sent by Apple. With those details, the attackers can gain access to the victim’s iCloud account and remove the Apple ID linked to the stolen device.
The Anatomy of the Trap
The modus operandi reflects a careful understanding of both human psychology and device security.
The first stage begins with target selection. Unlike mass phishing campaigns that are sent indiscriminately, this campaign appears to focus on a narrower group: people whose iPhones have recently been lost or stolen. The perpetrators may already possess the physical device, making the attack more dangerous because the phishing attempt is not random; it is linked to a real incident in the victim’s life.
The second stage is the delivery of the phishing SMS. The advisory notes that such messages may come from mostly numeric SMS headers and may impersonate Apple Support or Apple’s device-location services. The wording is crafted to push the victim toward quick action, often by suggesting that the device may be erased, secured or recovered if the user follows the link.
The third stage is the fake portal. The victim is redirected to a fraudulent website that closely resembles Apple’s official iCloud or Apple Support login page. Such pages often rely on deceptive domain names, familiar layouts and the visual language of legitimate technology platforms. To a distressed user trying to recover a missing phone, the difference between a genuine page and a counterfeit one may not be immediately obvious.
The final stage is the takeover. Once the victim provides credentials and OTP details, the attackers may access the iCloud account, disable security protections, remove the stolen device from the linked Apple ID and make the phone easier to resell, reuse or move through illicit markets.
Why This Scam Is Especially Effective
The campaign stands out because it exploits a moment when victims are least likely to behave cautiously. A person who has lost a phone is often anxious, hurried and desperate to prevent misuse of personal data. A message claiming to come from Apple Support or “Find My iPhone” arrives at precisely the moment when it seems most believable.
This is a familiar pattern in cybercrime: attackers do not merely exploit technical loopholes; they exploit timing, fear and trust. In this case, the trust is built around Apple’s reputation for security and the familiarity of services such as Find My iPhone. The victim may assume that any message about a missing device must be part of the recovery process.
The use of OTP harvesting also shows how cybercriminals are adapting to stronger security systems. Two-factor authentication is meant to protect users even when passwords are compromised. But when victims are tricked into voluntarily entering the OTP on a fake website, that additional layer of security can be bypassed.
For criminals, removing the Apple ID from a stolen phone is particularly valuable. A device locked to an Apple ID is harder to use or resell. By tricking the owner into giving access, the attacker can weaken the very security feature designed to protect the device after theft.
What Users Should Do After Losing a Device
The advisory recommends that users treat all SMS links relating to lost or stolen devices with caution, especially when the message comes from unfamiliar, numeric or international headers. Users should manually verify any URL before entering credentials and should avoid clicking links received through unsolicited messages.
For Apple users, the safest route is to use the official Find Devices page directly: https://www.icloud.com/find. Users should not remove a device from their Apple ID unless they have verified the request through official channels and fully understand the consequences. Keeping “Find My iPhone” active is an important part of protecting a missing device.
Victims should also avoid entering OTPs or two-factor authentication codes on unverified websites and should never share such codes with anyone. Strong passwords, active two-factor authentication and regular device updates remain basic but essential protections.
In India, lost or stolen mobile phones may also be reported for blocking through the CEIR portal, while phishing attempts and cybercrime incidents should be reported immediately at https://cybercrime.gov.in/ or by calling 1930.
The warning is ultimately about more than one phishing campaign. It is a reminder that the theft of a phone can quickly become the theft of an account, an identity and a wider digital life. In such moments, the most convincing message may also be the most dangerous one.


