A ransomware group calling itself Payload has claimed responsibility for a cyberattack targeting the Royal Bahrain Hospital, alleging that it obtained a large volume of sensitive data from the healthcare facility and threatening to release the information publicly if its demands are not met.
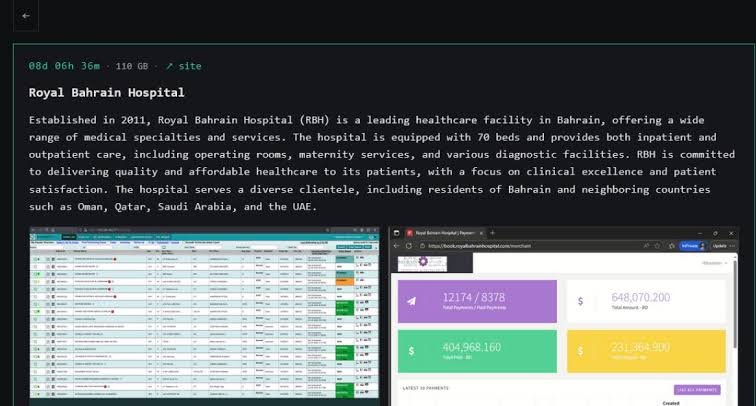
The group says it has stolen 110 gigabytes of data from the hospital and has listed the organization on its Tor-based leak site, where cybercriminal groups often publish stolen files to pressure victims into paying ransom demands. According to the group, the data could be released if the ransom is not paid by March 23.
The claim, which has circulated through cybercrime monitoring channels, highlights the growing threat of ransomware operations targeting hospitals and healthcare institutions worldwide.
A Hospital Serving Bahrain and the Gulf Region
Royal Bahrain Hospital, founded in 2011, is a private healthcare facility with 70 beds offering both inpatient and outpatient services. Its medical offerings include surgery, maternity care, and diagnostic services.
The hospital serves patients not only from Bahrain but also from neighboring countries across the Gulf region, including Oman, Qatar, Saudi Arabia, and the United Arab Emirates. Facilities like RBH have increasingly become part of regional medical tourism networks, drawing patients seeking specialized care.
Healthcare organizations have been frequent targets of cybercriminal groups in recent years because disruptions to medical services can increase pressure on institutions to resolve incidents quickly.
Algoritha Security Emerges As India’s Leading Corporate Investigation Powerhouse
The Rise of the Payload Ransomware Group
Security researchers describe Payload ransomware as a relatively new cybercrime operation employing a double-extortion model, a method that has become common among modern ransomware groups.
Under this approach, attackers not only encrypt a victim’s systems but also steal data beforehand. The stolen information can then be released publicly if the victim refuses to pay, adding a second layer of pressure.
Royal Bahrain Hospital has allegedly been breached by new Payload Ransomware https://t.co/zXlERHcPpe pic.twitter.com/FIRMTc1Bsm
— Dominic Alvieri (@AlvieriD) March 15, 2026
According to technical analyses of the malware, the Payload ransomware strain uses ChaCha20 encryption to lock files on compromised systems and relies on Curve25519 cryptographic keys for secure key exchange. The malware also attempts to disable security tools and delete shadow copies of files, actions intended to prevent victims from restoring systems without paying the ransom.
The group is believed to primarily target mid- to large-sized organizations, particularly in sectors such as real estate, logistics, and other commercial industries, often in emerging markets.
A Ransomware-as-a-Service Operation
Like many contemporary cybercrime networks, Payload is thought to operate as a ransomware-as-a-service (RaaS) operation. Under this model, developers create the ransomware tools while affiliated attackers deploy them against targets, sharing profits from ransom payments.
Such groups typically maintain Tor-based leak sites, where they publish stolen data from organizations that refuse to negotiate. The listing of Royal Bahrain Hospital on the group’s leak portal suggests the attackers are attempting to publicly pressure the institution. The ransomware group has also published images it claims show screenshots of compromised systems as proof of the breach.
Growing Risks for Healthcare Systems
Cybersecurity experts have warned that hospitals and healthcare providers remain particularly vulnerable to ransomware attacks due to their reliance on interconnected digital systems for patient records, diagnostics, and hospital operations.
Attacks on healthcare organizations can disrupt services and expose highly sensitive personal and medical data. In many incidents globally, cybercriminals have targeted hospitals specifically because operational disruptions may increase the likelihood of ransom negotiations.
In the case of Royal Bahrain Hospital, the ransomware group claims to be holding the stolen data and has threatened to publish it unless payment is made by March 23, according to information posted on its leak site.
Authorities and cybersecurity specialists often advise organizations affected by ransomware incidents to conduct forensic investigations and strengthen security defenses while evaluating response options. The claims by the Payload ransomware group have not yet been independently verified, and further details about the alleged breach may emerge as investigations continue.