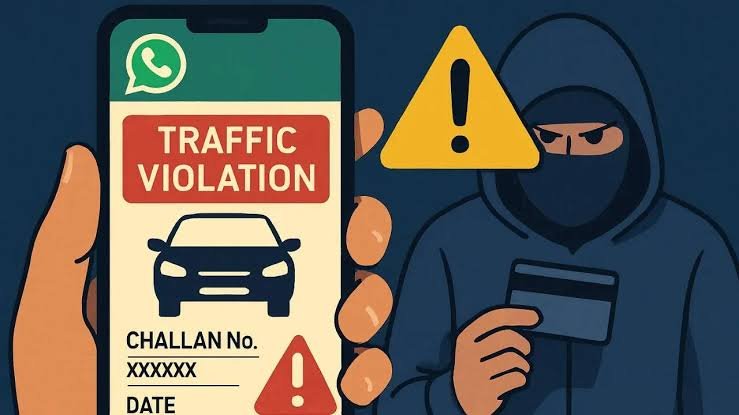
Mumbai Cyber Police have arrested a Surat-based businessman for masterminding a malicious APK scam that duped vehicle owners with fake RTO challans, siphoning ₹21 lakh through panic‑induced payments. The December operation exposes a surge in transport‑themed malware targeting India’s 35 crore+ registered vehicles.
Malicious APK Lures Drivers to Phantom Fines
Victims received SMS alerts claiming unpaid RTO fines with threats of vehicle seizure or licence suspension. Clicking led to a trojanised Android APK mimicking the Parivahan portal, granting fraudsters remote banking access. Funds routed via 50+ UPI mules across Gujarat-Maharashtra, masked as “fine payments.”
Arrested accused, Alpesh Patel (38), a Surat trader, developed and distributed the APK via 200+ WhatsApp groups and shady Google Play clones. Police seized 5 laptops, 12 burner phones and ₹3.5 lakh cash from his Vastrapur den.
Panic‑Button Payments Fuel ₹21 Lakh Haul
Scam peaked October-December 2025, netting 1,200+ downloads and 450 successful drains averaging ₹4,500 each. Forensic analysis by Mumbai Cyber Lab revealed keylogging, OTP interception and screen overlays mimicking RTO interfaces. Patel’s ledger tracked “challan IDs” to victim wallets, hawala’d to Dubai contacts.
Mumbai DCP (Cyber) Rashmi Karandikar confirmed interstate linkages, with Gujarat Police raiding 3 Surat associates. FIR under IT Act 66C/D, BNS 318 invokes PMLA for laundering probe.
RTO‑Branded Malware: Transport Sector’s New Nightmare
India’s e‑challan surge births sophisticated spoofs—fake apps harvest RC details via camera scans, auto‑populating “dues.” Parallel raids busted Delhi “fine generators” using AI voice clones as RTO officers. Transport Ministry warns: verify via official mParivahan app only.
Victim recovery stands at 12%, underscoring UPI’s fraud vulnerability despite RBI caps. Cyber cells push device fingerprinting and geo‑verified payments.
Lessons for India’s Digitised Drivers
This Surat sting highlights APK risks: sideloading malware evades Play Protect. Defences—app permissions audit, e‑challan checks via digilocker.gov.in, 1930 helpline. Mumbai Cyber’s Operation APK Shield vows nationwide mule hunts.
As vehicle digitisation accelerates, Patel’s fall signals crackdown: fake fines face real handcuffs.