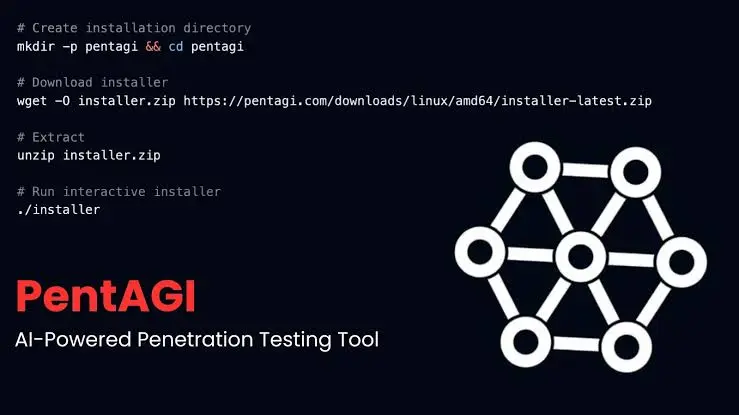
A new entrant in the cybersecurity landscape is challenging traditional models of penetration testing. PentAGI, an open-source platform, has been introduced as a fully autonomous “AI red team” system designed to simulate end-to-end security assessments without human intervention.
Unlike conventional tools that assist individual analysts, PentAGI operates as a coordinated system of artificial intelligence agents. Researchers describe it as a virtual security firm composed entirely of software entities, each responsible for a different phase of the attack lifecycle.
The platform has quickly gained attention, attracting thousands of users and contributors on GitHub. Its emergence reflects a broader trend in cybersecurity toward automation, where tasks traditionally performed by teams of experts are increasingly being delegated to machine-driven systems.
FCRF Launches Premier CISO Certification Amid Rising Demand for Cybersecurity Leadership
A System of Specialized Agents
At the core of PentAGI is a multi-agent architecture designed to replicate the workflow of a professional red team. An orchestrator agent oversees the operation, planning and sequencing the attack chain based on defined objectives.
Supporting this central agent are several specialized components. A researcher agent gathers intelligence from publicly available sources, including search engines and vulnerability databases. A developer agent generates custom exploit code tailored to identified weaknesses. An executor agent then deploys a suite of established security tools, such as network scanners and exploitation frameworks, to carry out the planned actions.
🚨 BREAKING: The cybersecurity industry is about to get completely disrupted.
Someone just open-sourced a fully autonomous AI Red Team.
It’s called PentAGI. 8,200+ stars on GitHub.
Not one AI agent. An entire simulated security firm. Researchers, developers, pentesters, and… pic.twitter.com/hyxCZvSfDq
— Guri Singh (@heygurisingh) March 21, 2026
These agents operate in coordination, sharing information and adapting their approach as new data becomes available. The system also includes a memory component that records outcomes from previous engagements, allowing it to refine its strategies over time.
Infrastructure, Isolation, and Workflow
PentAGI executes its operations within sandboxed Docker containers, a design choice intended to ensure isolation and manage risk. Each task is assigned a specific container environment, with the system automatically selecting the appropriate configuration.
This containerized approach allows the platform to run multiple processes in parallel while maintaining separation between them. It also mirrors industry practices in secure testing environments, where isolation is used to prevent unintended consequences during vulnerability assessments.
In addition to its execution framework, the platform incorporates a knowledge graph powered by Neo4j. This system maps relationships between targets, vulnerabilities, tools, and techniques across different tests, creating a structured repository of insights that informs subsequent operations.
Cost, Accessibility, and Industry Implications
Developers of the platform emphasize its accessibility. PentAGI is released under an MIT license and is available free of charge, in contrast to traditional red team engagements that can cost tens of thousands of dollars per project.
In the cybersecurity industry, comprehensive penetration testing often involves teams of specialists and significant financial investment. By automating these processes, platforms like PentAGI could alter how organizations approach security assessments, particularly for smaller firms with limited resources.
At the same time, the system’s capabilities highlight ongoing shifts in the field, where artificial intelligence is increasingly integrated into both defensive and offensive cybersecurity tools. PentAGI’s design—combining automation, modularity, and iterative learning—illustrates how established workflows are being adapted into software-driven models.
As the platform continues to gain visibility, its development and adoption are likely to be closely watched by both security professionals and organizations seeking new approaches to risk assessment.