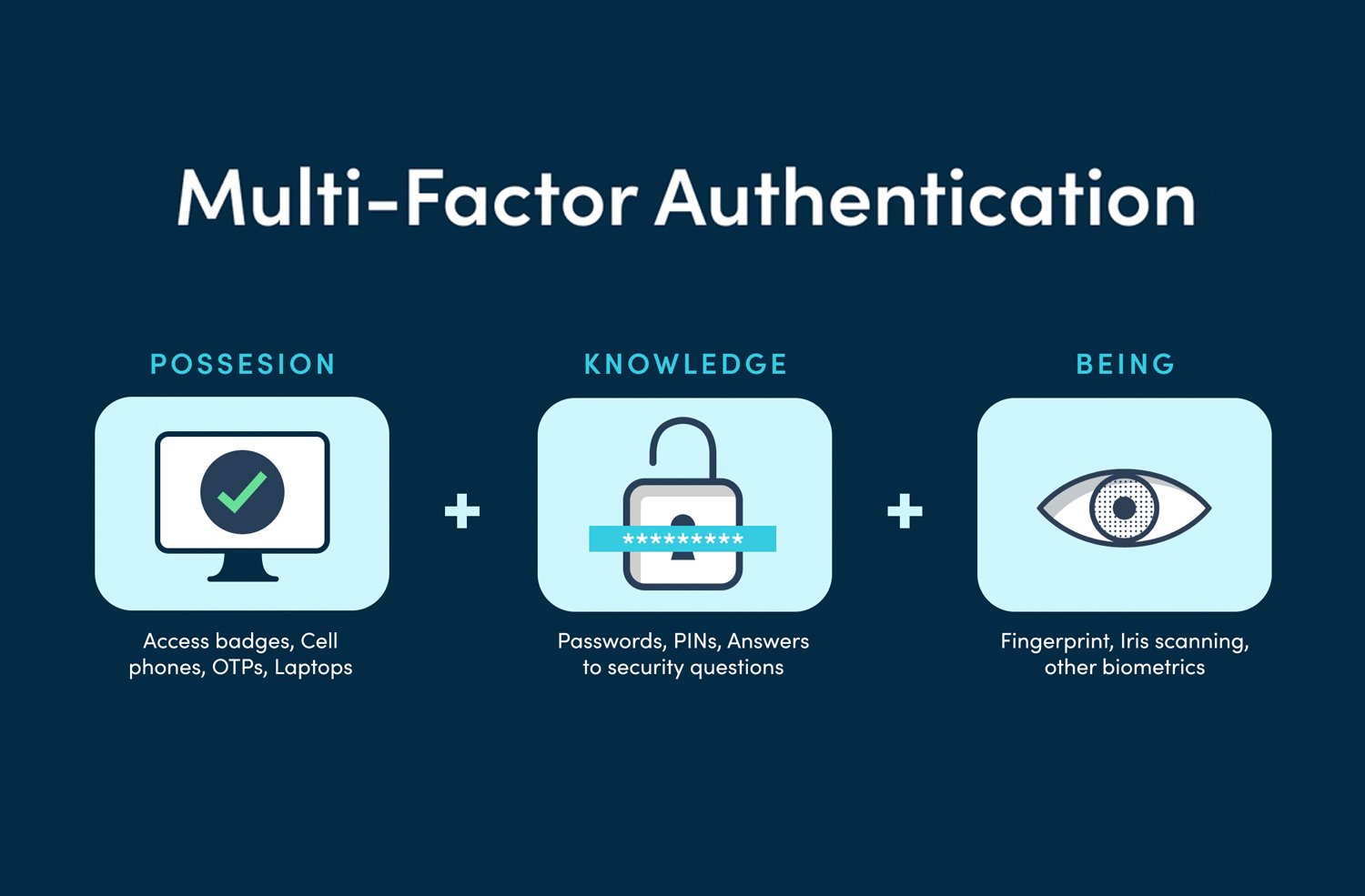
A single cybercriminal has reportedly compromised data from around 50 global organizations — and cybersecurity analysts say the root cause is shockingly simple: Multi-factor authentication (MFA) wasn’t turned on.
According to Israeli cybersecurity firm Hudson Rock, sensitive corporate files are now listed — and in some cases already sold — on the dark web. Victims span sectors such as aviation, utilities, robotics, law, and government infrastructure.
The attacker, known online as “Zestix” or “Sentap,” used credentials harvested by infostealer malware. Once usernames and passwords were collected, access to enterprise cloud portals became easy because MFA protections were missing.
“No exploits, no cookies just a password,” Hudson Rock noted in its report.
Final Call: FCRF Opens Last Registration Window for GRC and DPO Certifications
How the Attack Worked: Not Breaking In Just Logging In
Employees reportedly downloaded files laced with infostealer malware such as RedLine, Lumma, and Vidar. These tools quietly extract:
- saved passwords
- browser session data
- synced credentials
Armed with these stolen logins, the attacker specifically targeted enterprise file-sharing platforms, including: Progress Software ShareFile, Nextcloud, OwnCloud
Because most targeted organizations did not enforce MFA, the hacker could simply sign in like a legitimate user no sophisticated exploit required.
Progress Software confirmed that the breaches did not stem from vulnerabilities in its platform, but from valid credentials being reused without MFA safeguards.
High-Value Victims and Extremely Sensitive Data
Among the reported victims:
| Organization | Country | Sector | Nature of Exposed Data |
|---|---|---|---|
| Pickett and Associates | United States | Engineering / Power Utilities | Engineering data linked to major power utilities and critical infrastructure projects |
| Sekisui House | Japan | Real Estate / Construction | Homebuilding plans, development data, and internal project documentation |
| Iberia Airlines | Spain | Aviation | Fleet-related documents, safety manuals, and operational aviation data |
| CRRC MA | United States | Transport / Rail Systems | Transport system designs, signaling schematics, and engineering blueprints |
| Intecro Robotics | Turkey | Robotics / Defense | Aerospace and defense-related research and development files |
| Maida Health | Brazil | Healthcare | Medical records linked to families of the Brazilian Military Police |
| Burris & Macomber | United States | Legal Services | Legal strategies, internal documents, and customer records |
In several cases, datasets reportedly included:
- critical infrastructure blueprints
- confidential safety reports
- GPS coordinates for secure locations
- personal information, addresses and license details
- internal communications and legal documents
In one incident, engineering files for major U.S. utilities were allegedly advertised for 6.5 bitcoin, worth hundreds of thousands of dollars.
A Long-Standing Problem: Poor Credential Hygiene
Hudson Rock warned that some stolen credentials had been sitting in logs for years, never rotated or invalidated. Security researchers say this reflects a broader pattern:
- passwords reused across systems
- long-lived sessions never expired
- MFA not enforced even on sensitive accounts
Experts have repeatedly warned that attackers increasingly prefer logging in rather than hacking in a trend seen in major recent incidents involving healthcare, libraries, and cloud platforms.
What Security Experts Say Needs to Change
Cybersecurity analysts stress that MFA should be considered non-negotiable, especially on cloud systems. Recommended immediate actions for organizations include:
- enforce MFA across all remote and admin access
- regularly rotate passwords and revoke stale tokens
- scan for credentials found in infostealer logs
- educate employees about malicious downloads
- restrict access using zero-trust controls
Hudson Rock’s conclusion is blunt:
“It is time for organizations to enforce MFA and monitor compromised credentials.”
For many of the companies now facing data theft, the failure wasn’t due to sophisticated nation-state hacking it was simple negligence around basic authentication.
And as this case shows, sometimes one password is all it takes.