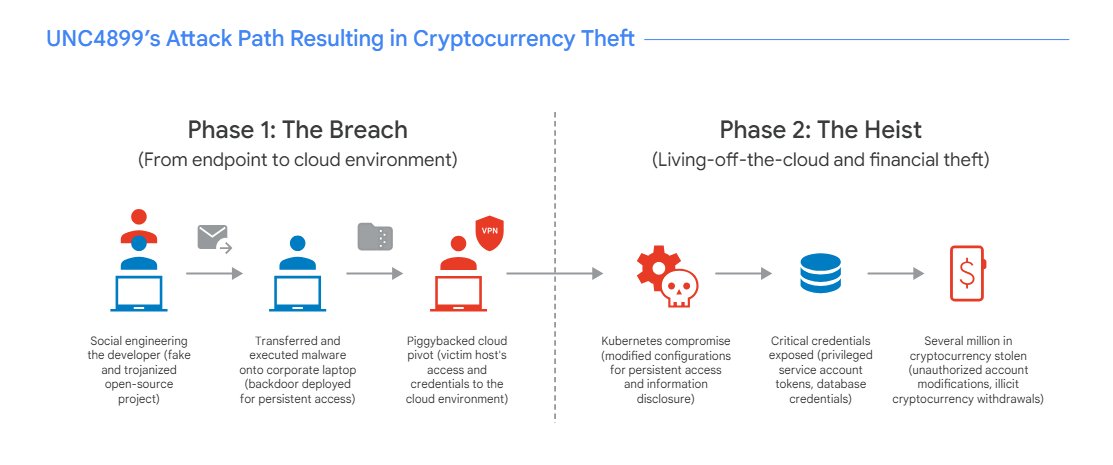
A cyber intrusion attributed to a suspected North Korean threat group reveals how attackers can move from a developer’s personal device to corporate cloud infrastructure, exploiting DevOps workflows to steal millions in cryptocurrency.
A Breach That Began on a Personal Device
A sophisticated cyberattack targeting a cryptocurrency organization appears to have begun with a deceptively simple step: a developer downloading what seemed to be a legitimate file.
According to security researchers at Google Cloud, the intrusion began when attackers used social engineering tactics to persuade the developer to download an archive file under the pretext of collaborating on an open-source project. The file was initially opened on the developer’s personal device before being transferred to the company’s corporate workstation using AirDrop.
Once inside the corporate environment, the file revealed its true purpose. When the developer interacted with the archive through an artificial intelligence–assisted integrated development environment, embedded malicious Python code was executed. The code installed a binary disguised as the Kubernetes command-line tool, allowing the attackers to establish a foothold inside the system.
The malicious binary connected to an attacker-controlled domain and functioned as a backdoor, enabling remote access to the developer’s machine and allowing the attackers to begin reconnaissance of the company’s cloud infrastructure.
Moving from Workstation to Cloud Infrastructure
From that initial entry point, the attackers pivoted toward the organization’s Google Cloud environment. Using authenticated sessions and available credentials, the threat actors began gathering information about the company’s cloud services and internal projects. Their reconnaissance ultimately led them to a bastion host—a secure server typically used to manage access to protected systems.
Investigators found that the attackers modified the bastion host’s multi-factor authentication policy to gain access and continue exploring the environment. This access allowed them to navigate between Kubernetes pods running within the company’s cloud infrastructure.
Security analysts described the operation as a carefully staged progression, beginning with a compromised workstation and expanding into the broader cloud environment.
Exploiting DevOps Workflows and Kubernetes
After gaining deeper access, the attackers began manipulating elements of the organization’s DevOps infrastructure.
According to Google Cloud’s analysis, the threat group altered Kubernetes deployment configurations to ensure persistence within the system. The modified configurations caused a bash command to run automatically whenever new pods were created. That command downloaded additional backdoor software, enabling continued control over the environment.
The attackers also targeted the organization’s continuous integration and continuous deployment platform. By modifying Kubernetes resources tied to the CI/CD environment, they were able to inject commands that exposed service account tokens in system logs.
With these tokens in hand, the attackers gained access to a high-privileged CI/CD service account. That access enabled them to escalate privileges and move laterally across the infrastructure, including reaching a pod responsible for managing network policies and load balancing.
At another stage of the attack, the stolen service account credentials were used to authenticate to a sensitive infrastructure pod operating in privileged mode. This allowed the attackers to break out of container restrictions and deploy another backdoor to maintain persistent access.
Database Manipulation and Cryptocurrency Theft
As the attack progressed, the intruders focused on systems that handled customer information and financial data.
According to Google Cloud, the attackers were able to extract database credentials that had been stored insecurely within environment variables inside a Kubernetes pod. Those credentials were then used to connect to the production database through the Cloud SQL Auth Proxy.
Once inside the database, the attackers executed SQL commands that altered user account settings. The modifications included password resets and updates to multi-factor authentication seed values associated with several high-value accounts.
With control over those accounts, the attackers ultimately withdrew digital assets worth several million dollars. Security researchers attributed the activity with moderate confidence to a North Korean threat group known as UNC4899, which has also been tracked under several other names, including Jade Sleet, PUKCHONG, Slow Pisces, and TraderTraitor.
A Complex Attack Chain
Google Cloud said the operation illustrates a complex attack chain that blends social engineering with cloud-specific exploitation techniques. The campaign relied on personal-to-corporate device transfers, cloud credential harvesting, container escape tactics, and the manipulation of DevOps workflows to gain deep access into the victim’s environment.
Researchers described the intrusion as a “living-off-the-cloud” operation, in which attackers leverage legitimate tools and infrastructure features to maintain persistence and evade detection.
The company noted that such attacks highlight the risks posed by peer-to-peer data transfer between personal and corporate devices, privileged container environments, and the insecure storage of secrets in cloud deployments.
To reduce the impact of similar incidents, Google Cloud recommended that organizations adopt layered security strategies, including strict identity validation, phishing-resistant multi-factor authentication, monitoring of container activity, and stronger management of sensitive credentials in cloud environments.