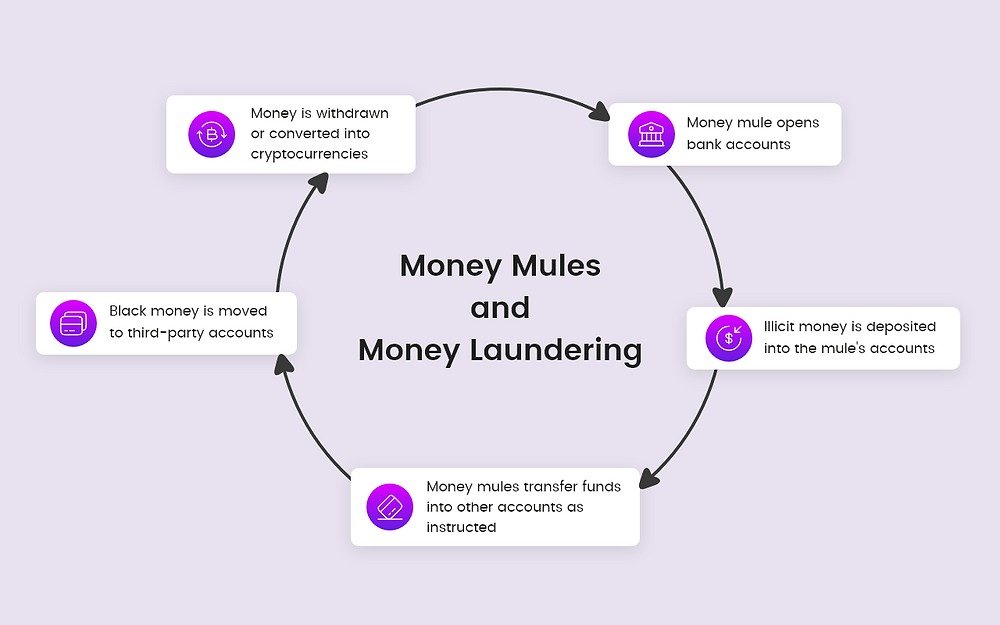
The nature of fraud in India’s digital economy is changing rapidly. Mule networks have emerged as the biggest fraud threat, identified as the most difficult to detect by 48% of companies, while social engineering ranked second at 33%.
Why Mule Networks Are So Dangerous
Mule networks are designed to appear legitimate at every touchpoint. They distribute funds across large clusters of connected accounts, making them extremely difficult to detect without cross-platform visibility.
Fraud losses in the banking sector have surged to ₹36,014 crore. This growth reflects that fraud operations are now faster, more organized, and industrialized. Criminals are leveraging real-time payments, instant onboarding, and interconnected digital platforms to scale their attacks.
FCRF Launches Premier CISO Certification Amid Rising Demand for Cybersecurity Leadership
For cyber risk teams, this has become a significant operational challenge. 58% of organizations identified false positives as a primary risk, meaning teams spend a substantial portion of their time investigating legitimate users while sophisticated fraud methods go undetected.
Identity, Compliance, and Detection Gaps
In 2025, identity became the main entry point for fraud in India’s digital economy. Fragmented and reusable identity data was increasingly misused at scale. As a result, organizations identified decision error as the biggest risk, as distinguishing genuine users from fraudsters has become more difficult.
Experts Push for Graph‑Based Anti‑Fraud Systems
Prof. Triveni Singh, renowned cybercrime expert and former IPS officer, said, “The real threat today comes from the network effect. When you analyze identities and devices across different platforms, you see that the same fraud patterns, tools, and behaviors are reused repeatedly. Therefore, relying solely on isolated data points is no longer sufficient.”
Fraud-as-a-Service and dark web toolkits are also making fraud more accessible and scalable for even low-skilled criminals. These toolkits provide stolen personal data, malicious APIs, and ready-to-use scam scripts.
Compliance practices are further contributing to the risk. Only 20% of organizations treat compliance as a strategic tool, while 50% view it merely as a regulatory obligation or a shield against reputational damage.
Fraud now moves across networks and organizations, making isolated controls insufficient. Risk teams require detection systems that integrate device, behavioral, and contextual intelligence across platforms. Graph analysis can map relationships between identities, devices, and transactions, helping uncover coordinated fraud activity that would otherwise appear legitimate in isolation.
Cyber experts emphasize that to combat such fraud, organizations must adopt adaptive anti-fraud systems, continuous monitoring, and technology-driven vigilance, ensuring customers—especially first-time digital users—remain protected.
About the author – Ayesha Aayat is a law student and contributor covering cybercrime, online frauds, and digital safety concerns. Her writing aims to raise awareness about evolving cyber threats and legal responses.