Cybersecurity researchers have uncovered a phishing campaign that manipulates Microsoft OAuth authentication links to deliver malware. By abusing legitimate identity platforms and disguising malicious downloads within ZIP archives, attackers are able to execute multi-stage infections that establish remote command-and-control access on victims’ systems.
Phishing Links Disguised as Legitimate Login Requests
A recent investigation by Microsoft has revealed a sophisticated phishing operation that exploits legitimate authentication mechanisms to deliver malware to unsuspecting users. The campaign uses carefully crafted URLs associated with widely used identity platforms, including Entra ID and Google Workspace, to redirect victims to malicious destinations while appearing legitimate.
According to Microsoft, attackers manipulated parameters within OAuth authentication requests to enhance the credibility of their phishing pages. In particular, the “state” parameter — typically intended to correlate request and response values during authentication — was repurposed by threat actors to carry encoded email addresses. By passing the victim’s email address through this parameter using various encoding techniques, the phishing page could automatically populate the target’s email field, giving the impression that the page was part of a legitimate login flow.
Security analysts said the tactic helps reduce suspicion among recipients who encounter pre-filled login forms that appear tailored specifically for them.
“The state parameter is intended to be randomly generated,” Microsoft noted, “but in these cases it was repurposed to carry encoded email addresses.”
The links were distributed through large-scale email campaigns designed to mimic routine digital interactions, including document signature requests, Microsoft Teams recordings, financial notifications and social-security related messages. In many cases, the links appeared directly in email messages or were embedded inside PDF attachments.
OAuth Abuse and Redirects to Attacker-Controlled Domains
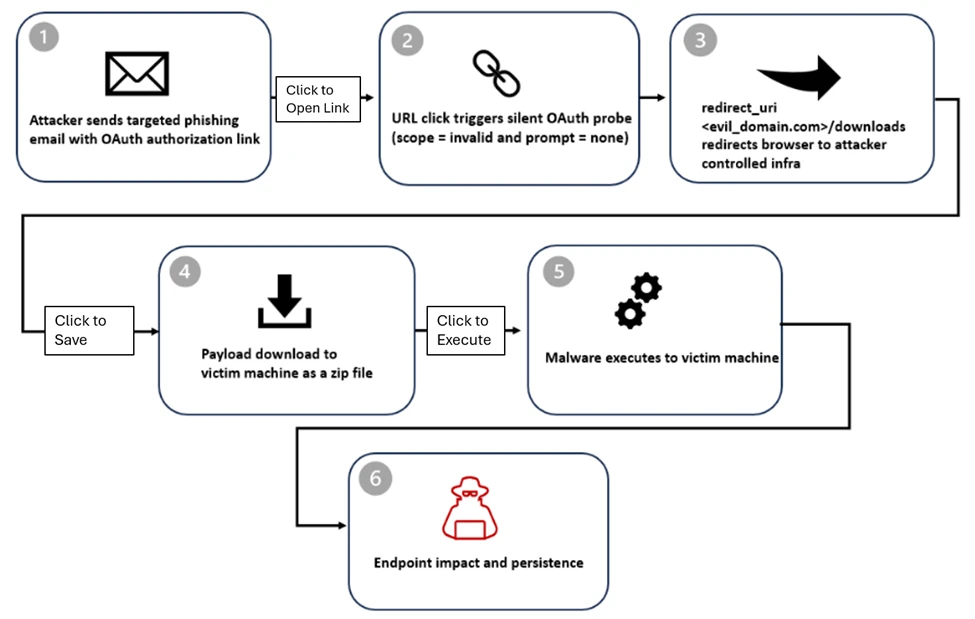
The attack sequence begins with the creation of a malicious application registered within an attacker-controlled tenant. The application is configured with a redirect URL pointing to a rogue domain hosting malware.
Once the infrastructure is in place, attackers distribute OAuth phishing links instructing recipients to authenticate with the malicious application. The links use intentionally invalid permission scopes, which trigger redirects during the authentication process.
These manipulated URLs exploit the trust users place in identity providers. Because the links reference recognizable authentication systems, recipients may assume they are part of legitimate login processes.
Microsoft researchers said the technique enables attackers to generate URLs that appear benign but ultimately redirect users to malicious landing pages. Some campaigns were also found to route victims through phishing frameworks such as EvilProxy, an adversary-in-the-middle toolkit designed to intercept login credentials and session cookies during authentication.
The use of such frameworks allows attackers to capture authentication data even when victims attempt to sign in through trusted identity platforms.
Multi-Stage Malware Delivery Through ZIP Archives
Once redirected to attacker-controlled infrastructure, victims are prompted to download a ZIP archive containing the malicious payload. The archive typically includes a Windows shortcut file, or LNK, which triggers a PowerShell command when opened.
The PowerShell script initiates reconnaissance activity on the victim’s system, executing discovery commands to gather information about the host environment. The LNK file then extracts an MSI installer embedded within the archive.
During installation, the MSI drops a decoy document intended to distract the victim while the infection process continues in the background. At the same time, a malicious dynamic link library — identified as “crashhandler.dll” — is sideloaded using a legitimate executable named “steam_monitor.exe.”
The DLL then decrypts an additional file called “crashlog.dat,” which contains the final payload. This payload executes directly in memory, a technique commonly used to evade detection by security software.
Researchers said the final stage establishes an outbound connection to an external command-and-control server, enabling attackers to maintain remote access and potentially conduct further activity on compromised systems.
Security Response and Mitigation Measures
Following the investigation, Microsoft said it had removed several malicious OAuth applications that were linked to the campaign. The company also issued guidance to organizations on reducing exposure to similar attacks.
Security teams are advised to limit the ability of users to grant consent to third-party applications and to regularly review application permissions within their identity environments. Removing unused or excessively privileged applications is also recommended as part of routine security hygiene.
The company warned that the campaign demonstrates how legitimate authentication systems can be manipulated to deliver malware while appearing credible to victims. As attackers increasingly rely on trusted platforms and familiar workflows, security experts say organizations must monitor application permissions and authentication activity more closely to detect suspicious behavior before it leads to compromise.