A newly documented cyber-espionage campaign targeting Indian government entities has revealed a quietly evolving playbook: fake software updates, private GitHub repositories used as command-and-control infrastructure, and custom malware designed to evade both automated analysis and traditional antivirus tools. Researchers say the activity reflects a deliberate shift toward blending malicious operations with legitimate online services.
A Campaign Built on Familiar Trust
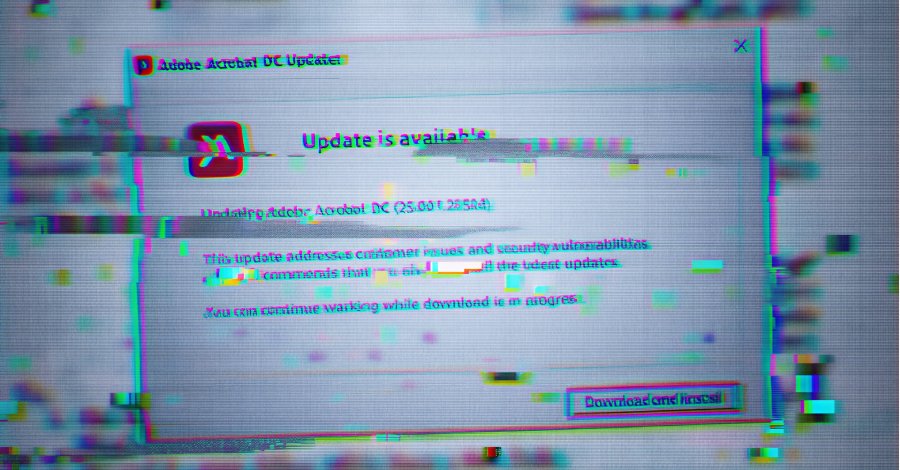
The campaign begins with deception that relies less on technical novelty than on user expectation. Victims are lured through phishing emails carrying PDF documents that appear benign at first glance. Embedded within them is a blurred image overlaid by a pop-up urging recipients to download an update for Adobe Acrobat Reader DC.
According to researchers at Zscaler ThreatLabz, the prompt is carefully engineered. Clicking “Download and Install” triggers the retrieval of an ISO image file, but only if certain conditions are met: the request must originate from an IP address located in India, and the browser’s user-agent string must indicate a Windows system. These server-side checks are designed to prevent automated security scanners from easily fetching the payload, ensuring the malicious file is delivered only to intended targets.
Once mounted, the ISO contains a Golang-based downloader dubbed GOGITTER, marking the beginning of a multi-stage infection chain.
Certified Cyber Crime Investigator Course Launched by Centre for Police Technology
GitHub as Command and Control
After execution, GOGITTER establishes persistence and prepares the system for remote control. The malware creates a Visual Basic Script (VBScript) file—if one does not already exist—across several common directories, including C:\Users\Public\Downloads, C:\Users\Public\Pictures, and %APPDATA%. This script is configured to poll two pre-defined command-and-control servers every 30 seconds for further instructions.
To ensure longevity, GOGITTER also creates a scheduled task that executes the VBScript every 50 minutes. In parallel, it checks for the presence of a file named adobe_update.zip. If the archive is missing, the malware downloads it from a private GitHub repository controlled by the attackers. Researchers noted that the GitHub account hosting the repository was created on June 7, 2025, underscoring how recently the infrastructure was set up.
This use of private GitHub repositories allows the attackers to camouflage malicious traffic within routine HTTPS connections to a widely trusted platform, complicating detection and attribution.
Lightweight Backdoors and Remote Execution
Within the downloaded archives is another Golang-based component, a lightweight backdoor known as GITSHELLPAD. Once deployed, it begins polling its command-and-control endpoint every 15 seconds by requesting a file named command.txt.
The backdoor supports a limited but functional set of commands. Operators can navigate directories, upload or download files, and execute arbitrary commands—either silently in the background or with captured output. When a command is executed, its results are written to a result.txt file and uploaded back to the GitHub repository via an HTTP PUT request. The original command.txt file is then deleted, reducing forensic traces.
In observed cases, attackers used this access to download additional RAR archives via command-line tools such as cURL. These packages included utilities for collecting system information and deploying further payloads, after which the tools were wiped from disk.
Obfuscation, Targeting, and Attribution
One of the most notable payloads observed in later stages is GOSHELL, a bespoke Golang loader used to deliver Cobalt Strike beacons. Zscaler researchers found that GOSHELL’s executable had been artificially inflated to approximately one gigabyte by appending junk data to its Portable Executable overlay—an apparent attempt to evade antivirus engines and sandbox analysis.
GOSHELL also incorporates host-based targeting. It checks the victim’s hostname against a hard-coded list and executes only if a match is found, further limiting exposure and reducing the risk of discovery in unintended environments.
Zscaler has linked the activity to two campaigns, which it has codenamed Gopher Strike and Sheet Attack, first identified in September 2025. While the techniques share similarities with those used by the Pakistan-linked advanced persistent threat group APT36, researchers assess with medium confidence that the operations may originate from a new subgroup or a parallel actor operating in the same ecosystem.
Together, the campaigns illustrate how modern espionage operations increasingly rely on legitimate platforms, selective targeting, and layered obfuscation—tools that favor patience and precision over speed or scale.