In a significant cyber incident, a foreign hacker reportedly accessed files on an FBI server at the New York field office in 2023. The server housed sensitive documents related to long-standing investigations into the controversial sex offender Jeffrey Epstein, according to sources familiar with the matter and recently published Department of Justice documents.
According to the sources, there was no indication of involvement by any foreign government; the breach appeared to have been carried out by an individual cybercriminal. The FBI described the incident as “an isolated cyber event,” adding, “We restricted access to the malicious actor and secured the network. The investigation is ongoing, so we have no further comments at this time.”
Academics and cybersecurity experts note the potential intelligence value of the Epstein files. Jon Lindsay, who researches emerging technology and global security at the Georgia Institute of Technology, said, “If foreign intelligence agencies are not targeting the Epstein files, that would be shocking. Russia or other states would certainly have an interest in this material.”
Breach Linked to Vulnerable Server at FBI Forensic Lab
The breach occurred on 12 February 2023, when a server at the FBI’s Child Exploitation Forensic Lab was inadvertently left vulnerable. Special Agent Aaron Spivack, navigating complex procedures for handling digital evidence, inadvertently exposed the server. The following day, upon powering on his computer, he discovered a text file warning that the network had been compromised.
Further investigation revealed unusual activity on the server, including attempts to access files related to the Epstein investigation. The timeline does not specify which files were accessed, whether the hacker downloaded any data, or the hacker’s identity.
FBI Reportedly Engaged Hacker Through Video Call
FBI officials reportedly engaged the hacker via a video chat. Sources said the hacker expressed disgust at the presence of child exploitation images on the server and threatened to expose the content to law enforcement. To defuse the situation, the FBI convinced the hacker that they were actually speaking to FBI personnel. The video chat involved showing law enforcement credentials, which reportedly pacified the intruder.
Internal Procedures and Conflicting Guidance
According to Spivack, contradictory guidance and procedural inconsistencies at the New York field office contributed to the vulnerability. He claimed to investigators that he was being made “a scapegoat for the intrusion.”
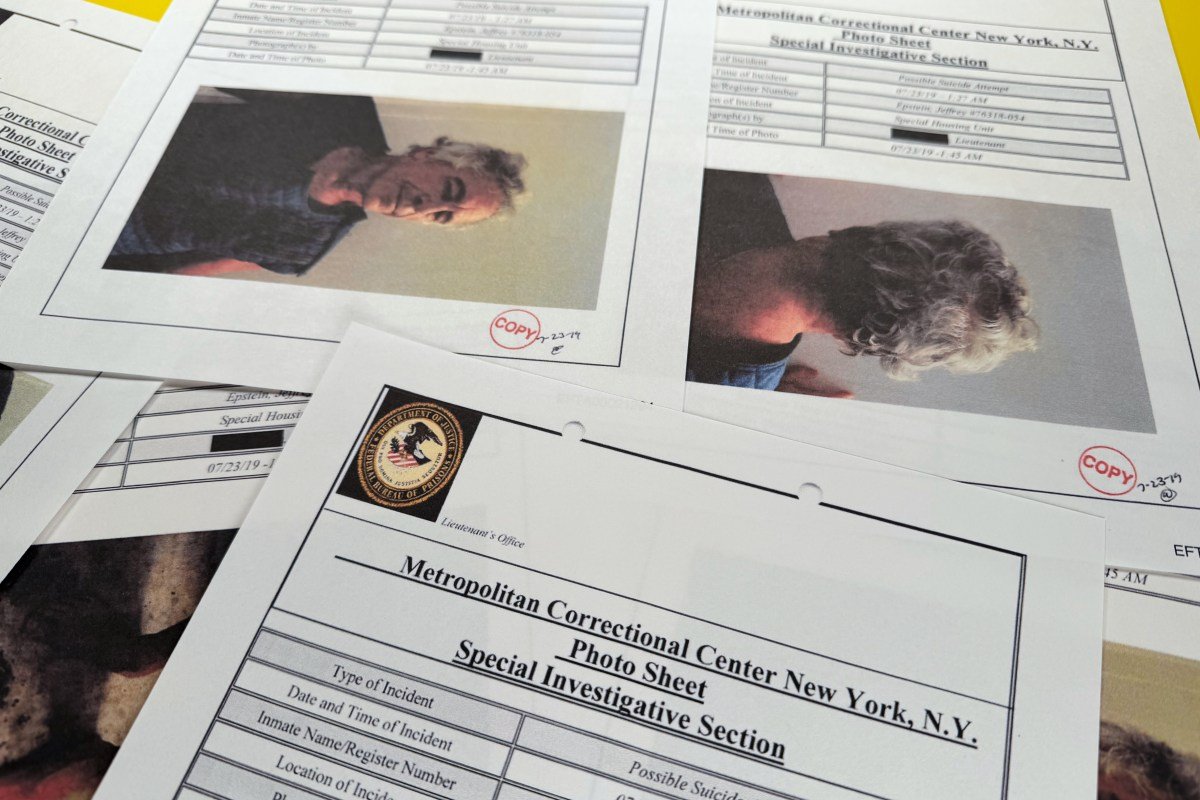
The FBI has not disclosed the hacker’s identity, location, or actions taken with the accessed material. Many portions of the documents are heavily redacted, and some remain completely confidential. The Trump administration previously stated that certain files were withheld to protect victims’ identities and ongoing investigations.
Epstein, long associated with Donald Trump, had pleaded guilty in 2008 to charges of prostitution, including solicitation of an underage girl. He was found hanged in his jail cell in 2019 in what was ruled a suicide following his arrest on federal sex trafficking charges.
Broader Questions About Cybersecurity Safeguards
The incident raises serious questions about the FBI’s internal cybersecurity measures and highlights broader global intelligence and cybersecurity concerns. Experts emphasize that sensitive data of this nature demands robust procedural safeguards and comprehensive digital security protocols to prevent similar breaches in the future.