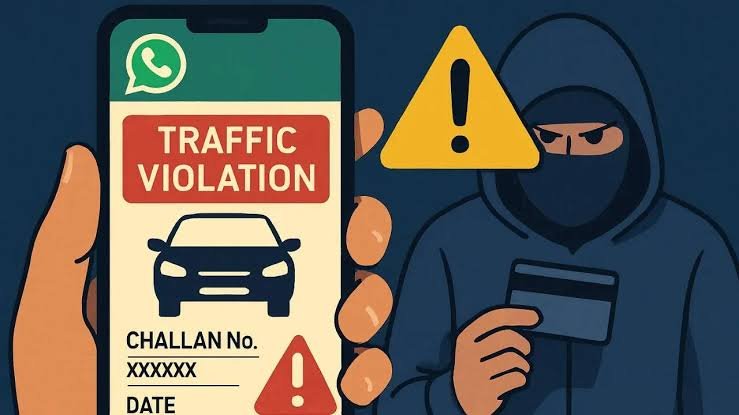
Subodh Rawat, a Kedarpuram resident, lost over ₹3.68 lakh in minutes after clicking a fraudulent RTO e-challan SMS link sent by cyber crooks. The scam highlights surging fake traffic fine phishing in Uttarakhand, with Nehru Colony police probing the multi-layered theft including broken fixed deposits. Victims face instant digital hijacks, underscoring urgent need for vigilance amid national scam waves.
Detailed Incident Timeline
On December 27, Rawat’s phone buzzed with an SMS posing as an official RTO challan notice, urging immediate payment via a suspicious link. Upon clicking, his device froze—a classic malware symptom—allowing remote access to banking apps and OTP interception. Scammers executed four swift transactions, exhausting his savings balance before liquidating two FDs for extra funds, totaling the hefty loss.
Rawat spotted the debit alerts pouring in and raced to secure his accounts, but damage was done in under 10 minutes. He filed complaints with the cyber helpline (1930) and Nehru Colony station, triggering an FIR under IT Act cyber fraud clauses. This mirrors Dehradun’s rising fraud reports, from investment cons to phishing, with locals losing crores yearly.
Police Investigation Underway
SHO Sanjeet Kumar’s team at Nehru Colony has launched a full probe, analyzing transaction trails, IP logs, and device forensics for international links common in such scams. Uttarakhand STF often joins for cross-border angles, as seen in prior Doon arrests tied to Dubai handlers. No suspects nabbed yet, but police urge similar victims to come forward for pattern matching.
How Fake RTO Scams Operate
Cybercriminals harvest vehicle data from public registries or prior leaks, crafting hyper-realistic SMS with personalized reg numbers and fine amounts. Links lead to phishing sites mimicking parivahan.gov.in, injecting keyloggers or overlay malware that captures credentials mid-session. Funds route through mule accounts—often rural Rajasthan or Bihar—before vanishing overseas, evading quick freezes.
Recent Cyble analysis flags a “scam wave” with browser exploits surging 300%, hitting 10,000+ Indians monthly via e-challan bait. Dehradun’s proximity to tech-savvy youth and retirees makes it prime turf, akin to Pune’s ₹50 lakh collective losses last quarter.
Legal Recourse and Victim Rights
Under Bharatiya Nyaya Sanhita Section 316 and IT Act 66D, penalties include 7+ years jail plus fines. Victims can seek bank refunds if reported within golden hour via 1930; Jharkhand HC recently mandated 24-hour freezes post-FIR. National Cyber Crime Portal tracks 1.2 lakh annual cases, recovering 10-20% via trails.
Expanded Prevention Guide
- Cross-check fines solely on official sites like echallan.parivahan.gov.in—bookmark to avoid phishing duplicates.
- Install reputable antivirus with anti-phishing (e.g., Avast, Kaspersky) and enable biometric logins over SMS OTPs.
- Monitor via bank apps’ real-time alerts; freeze cards instantly on suspicion through net banking.
- Educate family: Scammers spoof RTO numbers using VoIP; hang up and verify independently.
- For Uttarakhand users, join local awareness drives by Dehradun Cyber Cell—report patterns early.
About the author – Rehan Khan is a law student and legal journalist with a keen interest in cybercrime, digital fraud, and emerging technology laws. He writes on the intersection of law, cybersecurity, and online safety, focusing on developments that impact individuals and institutions in India.