Security researchers say compromised web-hosting control panels, particularly cPanel accounts, have become a thriving commodity in cybercriminal markets, enabling attackers to launch phishing campaigns, spam operations and data theft using trusted internet infrastructure.
The underground economy that supports cybercrime has increasingly begun to resemble conventional digital marketplaces. Researchers monitoring fraudulent online communities say that access to compromised web-hosting control panels — especially cPanel accounts — is now openly advertised and traded in bulk, turning stolen credentials into a standardized product for attackers seeking ready-made infrastructure.
In a recent analysis of activity across monitored fraudulent chat groups, security researchers from Flare documented more than 200,000 posts referencing cPanel access over a seven-day period, offering insight into how widely these credentials circulate in underground markets. The findings suggest that control panel access — once merely a byproduct of breaches — is increasingly treated as a standalone asset within cybercriminal supply chains.
As cybercrime operations grow more structured, researchers say that the sale of compromised hosting credentials reflects a broader shift toward access brokerage, where attackers monetize entry points into legitimate digital systems rather than building attack infrastructure themselves.
FCRF Launches Flagship Certified Fraud Investigator (CFI) Program
cPanel: A Gateway to Website Infrastructure
cPanel is among the most widely used Linux-based web hosting control panels globally, providing a centralized interface for managing website infrastructure. Through the panel, administrators can control domains, databases, email services, DNS configurations, SSL certificates and file systems.
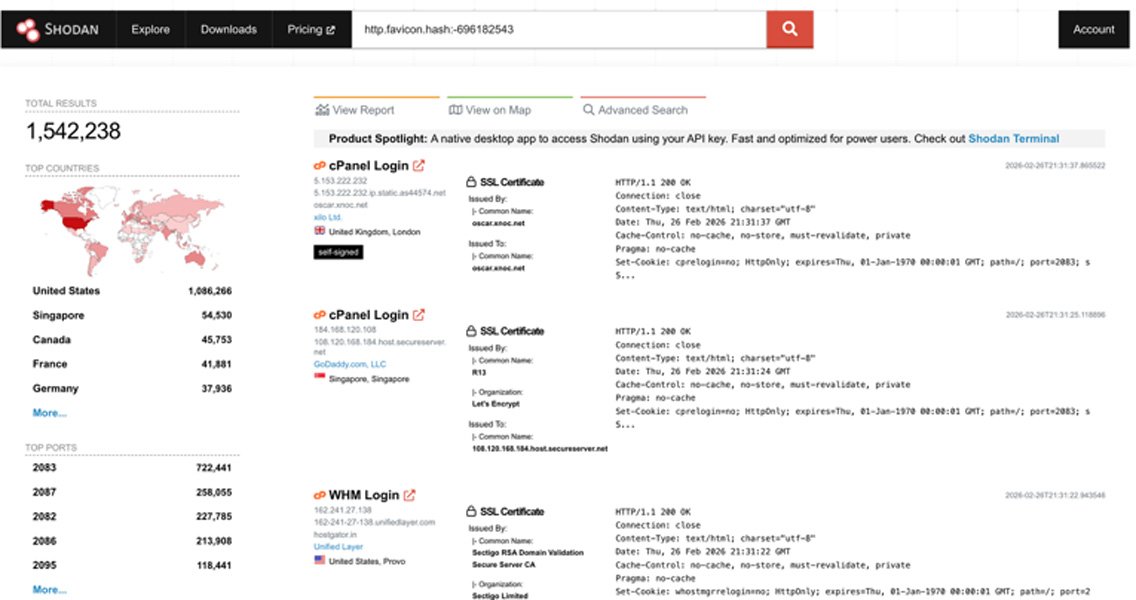
Because of its role as a management layer above core server services, access to a cPanel account effectively grants control over many elements of a website’s operational environment. According to internet-connected device search engines such as Shodan, more than 1.5 million servers connected to the internet run cPanel software.
Researchers say this centralization of administrative tools makes cPanel accounts attractive targets for attackers seeking efficient entry points into digital infrastructure.
Once an attacker gains valid login credentials, they can deploy malicious capabilities without necessarily exploiting additional vulnerabilities. Among the activities observed after account compromise are:
- Creating new administrative users to maintain persistence
- Uploading malware or web shells
- Deploying phishing kits as subdomains under legitimate websites
- Setting up SMTP mail accounts to distribute phishing or spam campaigns
- Attempting privilege escalation to obtain root access
- Extracting sensitive data stored in databases, including personal information or system credentials
In shared hosting environments, a single compromised control panel may also provide access to multiple domains hosted on the same server.
How Attackers Gain Access
Researchers note that the compromise of hosting control panels typically occurs through several common attack pathways. The most frequently observed method involves the theft or brute-forcing of login credentials.
Attackers often rely on credential abuse techniques such as phishing campaigns, password reuse from previous data breaches, and credential stuffing attacks, in which automated tools attempt large numbers of username-password combinations against exposed login portals.
Other entry points arise from weaknesses within the websites themselves. Vulnerable content management systems — including platforms such as WordPress, Joomla or Drupal — along with outdated plugins and themes can allow attackers to upload web shells or escalate privileges.
Misconfiguration also plays a role. Security researchers say that exposed configuration files such as .env or config.yaml, weak passwords, or the absence of multi-factor authentication can make hosting environments easier to compromise.
Once access is obtained, attackers may move laterally within the hosting environment, harvest additional credentials stored on the server, or modify system configurations to maintain control.
Over time, automated tools and botnets have expanded the scale of these activities, continuously scanning the internet for exposed login panels, known software vulnerabilities and misconfigured systems.
A Marketplace for Compromised Hosting Accounts
The research also points to a growing commoditization of hosting access in underground markets. In many forums and chat groups monitored by investigators, sellers openly advertise batches of compromised control panel credentials, often packaged and priced according to perceived quality.
Analysis of listings suggests that these credentials are frequently sold in bulk. A sample of advertised pricing included:
- Premium access: 100 accounts for $75
- Premium access: 500 accounts for $289
- Premium access: 1,000 accounts for $645
- Regular access: 1,000 accounts for $23
- Regular access: 3,000 accounts for $42
- Regular access: 5,000 accounts for $58
Researchers say such pricing structures resemble traditional wholesale markets, where the value of a product decreases as the quantity increases.
The classification of “premium” access generally reflects factors such as domain reputation, hosting provider credibility and search-engine trust metrics. Servers associated with reputable providers or domains with established credibility may command higher prices.
In contrast, domains using less trusted top-level domains — such as .xyz or .net — are often considered lower-value assets because phishing campaigns launched from them may achieve lower success rates.
Listings often promote compromised hosting panels using marketing language similar to legitimate technology sales, describing accounts as “fresh,” “high quality,” “spam clean,” or “ready for mailing.”
Researchers also observed that the same inventory is frequently reposted across multiple chat groups. In the seven-day sample analyzed, more than 90 percent of posts appeared to be duplicates, suggesting that sellers rely on automated reposting tools to amplify their listings across different channels.
Security Implications and Defensive Measures
Security specialists say the growing trade in hosting credentials reflects a broader evolution in cybercrime operations. Rather than developing complex exploits themselves, many attackers now purchase ready-made access to trusted infrastructure.
When compromised hosting accounts are used to distribute phishing campaigns or spam emails, the activity can originate from legitimate domains and IP addresses, increasing the likelihood that messages bypass security filters.
The consequences for affected organizations can extend beyond technical disruption. Researchers say compromised hosting environments may lead to domain or IP blacklisting, reputational damage, website defacement or even ransomware incidents if attackers encrypt hosted data.
To reduce these risks, security experts recommend a set of preventive measures for organizations operating hosting control panels:
- Enabling multi-factor authentication for administrative accounts
- Enforcing strong and unique passwords
- Restricting administrative login access by IP address when possible
- Monitoring outbound SMTP activity to detect spam abuse
- Implementing file integrity monitoring to identify unauthorized modifications
- Tracking suspicious activity such as new account creation, unexpected scheduled tasks or configuration changes
- Regularly patching content management systems and plugins
- Disabling unused services and applying the principle of least privilege
Researchers also emphasize monitoring credential exposure in stealer logs and underground marketplaces, where stolen credentials often surface after initial compromise.
As cybercrime increasingly revolves around access to legitimate infrastructure, they say the protection of hosting credentials has become a central defensive priority — not only to safeguard individual websites, but also to prevent their use as platforms for wider online fraud campaigns.