A cyber attack method known as “ClickFix” has made a disconcerting leap from Windows to Apple and Android platforms. Security researchers at c/side have revealed a sinister new version of ClickFix that now targets macOS, Android, and iOS systems raising red flags for cross-platform threats.
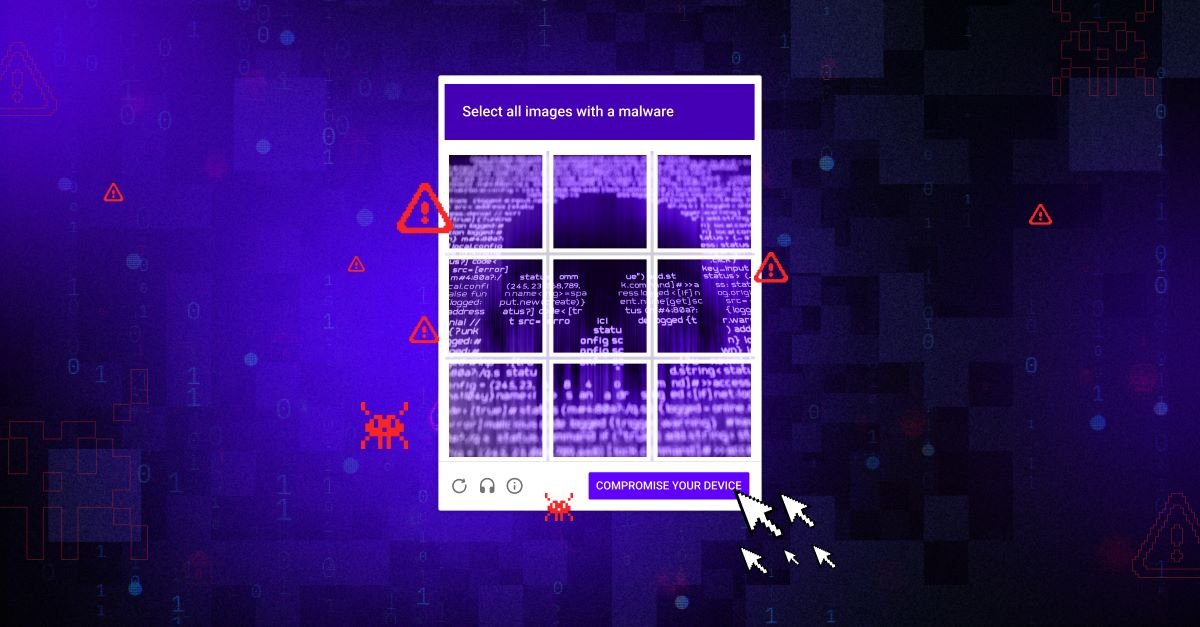
Previously a Windows-only scheme, ClickFix uses compromised websites that inject malicious JavaScript. Users are redirected to pages masquerading as URL shorteners or CAPTCHA prompts, urging them to copy links that trigger malware downloads. On macOS, victims are duped into running a shell script by pasting commands into the Terminal, often under the guise of verification steps. Android and iOS users face an even more dangerous scenario: malware delivered via drive-by downloads—simply visiting a site is enough to trigger installation of a malicious TAR archive, no clicks required.
Data Protection and DPDP Act Readiness: Hundreds of Senior Leaders Sign Up for CDPO Program
A Surge in Sophistication and Reach
This new ClickFix variant marks a significant shift in cybercriminal strategy—from mere technical exploit to layered psychological manipulation. It employs trusted infrastructures and mimics genuine interactions, allowing it to bypass traditional antivirus systems and user suspicions alike.
Mac users, already considered less vulnerable, are now being explicitly targeted. Separate campaigns have used ClickFix tactics disguised as fake CAPTCHA prompts to install the Atomic macOS Stealer (AMOS)—a malware strain that steals login credentials, crypto-wallet data, and more. Researchers have even identified expanded ClickFix attacks using AppleScripts coded for macOS, capable of harvesting passwords and personal data via typosquatted finance or app store domains.