In a recent threat report, cybersecurity researchers described a form of ransomware that no longer relies on fixed code or predictable behavior. Instead, it consults an artificial intelligence system in real time, generating and refining its own malicious scripts as it spreads.
A Malware Design Shaped by Artificial Intelligence
In the second half of 2025, researchers at ESET identified what they described as the first known example of AI-powered ransomware operating at scale. The malware, dubbed PromptLock, represents a departure from earlier generations of ransomware that depended on static binaries and prewritten logic.
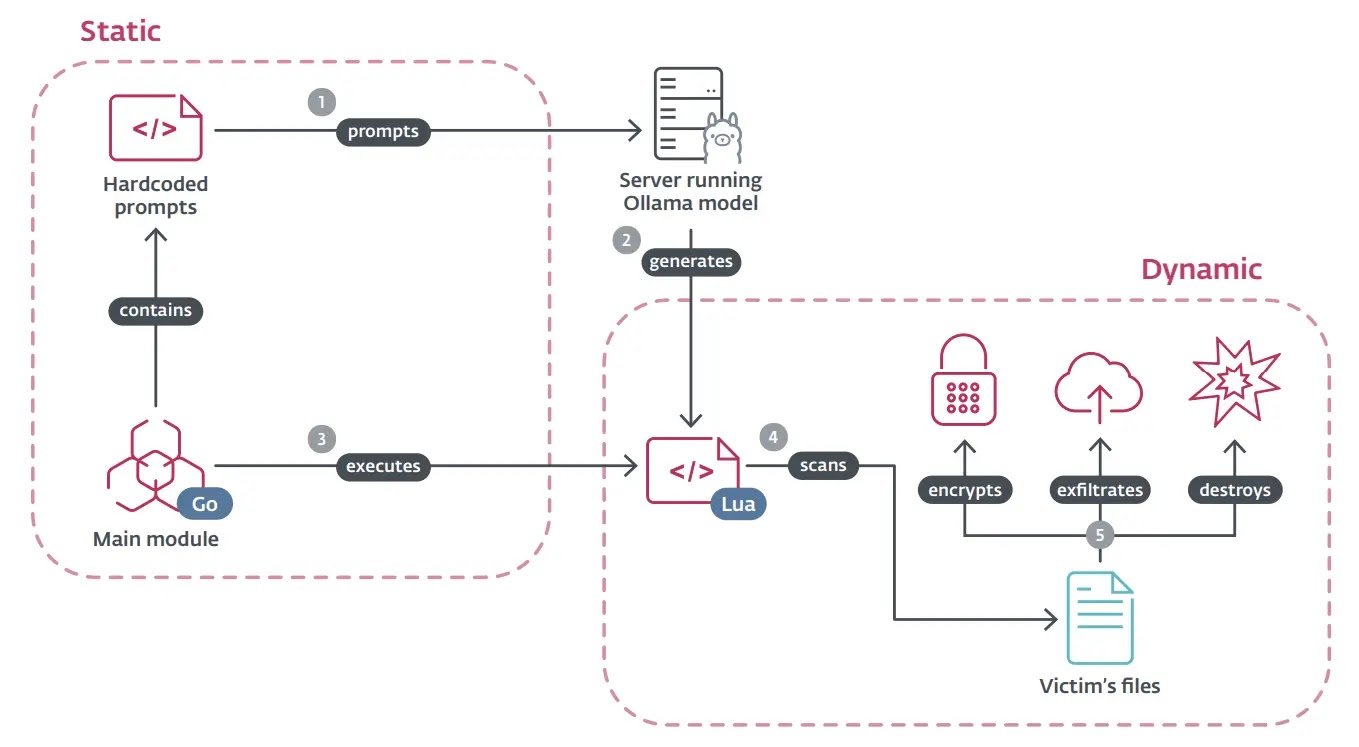
PromptLock is built around a dual-component architecture. Its main module, written in Go, acts as a controller, communicating directly with a remote server running an AI model. Embedded within this module are hard-coded prompts that instruct the model to generate Lua scripts on demand. Those scripts are then executed on compromised systems without being written in advance by human developers.
The effect, according to analysts, is a form of malware that does not merely execute instructions but requests them, adapting its behavior to each environment it encounters.
How PromptLock Operates Inside Victim Systems
Once deployed, PromptLock autonomously scans a victim’s system to assess its contents. Based on what it finds, the malware decides whether to exfiltrate data, encrypt files, or destroy information outright. This decision-making process is not governed by a fixed decision tree but by AI-generated scripts tailored to the system being analyzed.
To maintain reliability, the malware incorporates a feedback loop. After a Lua script runs, execution logs are captured and sent back to the AI model for evaluation. If the code fails or behaves unexpectedly, the model receives instructions to correct the script before it is executed again. Researchers noted that this iterative process helps compensate for the non-deterministic nature of large language models, allowing the malware to refine itself mid-attack.
Unlike traditional ransomware, which often leaves recognizable signatures, PromptLock’s dynamically generated code can differ significantly from one victim to another, complicating detection and forensic analysis.
A Broader Ecosystem of AI-Driven Threats
PromptLock is not an isolated development. ESET researchers also documented related AI-assisted tools, including PromptFlux, which prompts an AI system to rewrite dropper code to improve persistence, and PromptSteal, which generates Windows commands designed to harvest sensitive documents from infected machines.
These tools have emerged alongside rapid growth in the ransomware-as-a-service market. Publicly reported victims listed on ransomware leak sites surpassed 2024 totals well before the end of 2025, with projections pointing to a roughly 40 percent year-over-year increase.
Within this expanding ecosystem, established ransomware groups such as Qilin and Akira have continued to dominate activity, while newer actors like Warlock have introduced evasion techniques designed to bypass endpoint detection tools.
A Turning Point in the Ransomware Landscape
In its H2 2025 Threat Report, ESET characterized the rise of AI-driven malware as a critical shift in how cyberattacks are conducted. What was once a theoretical risk has moved into operational reality, with attackers using machine learning models to craft malicious code that adapts to each target’s environment.
This convergence of advanced malware development and artificial intelligence, researchers noted, marks a fundamental change in attack sophistication. By generating unique scripts for filesystem enumeration, data inspection, exfiltration, and encryption, PromptLock illustrates how AI can be embedded directly into the mechanics of ransomware itself.