Threat actors with alleged ties to Iran have compromised the personal email account of Kash Patel, the director of the Federal Bureau of Investigation, and released a cache of emails and documents online, according to statements from both the attackers and U.S. authorities.
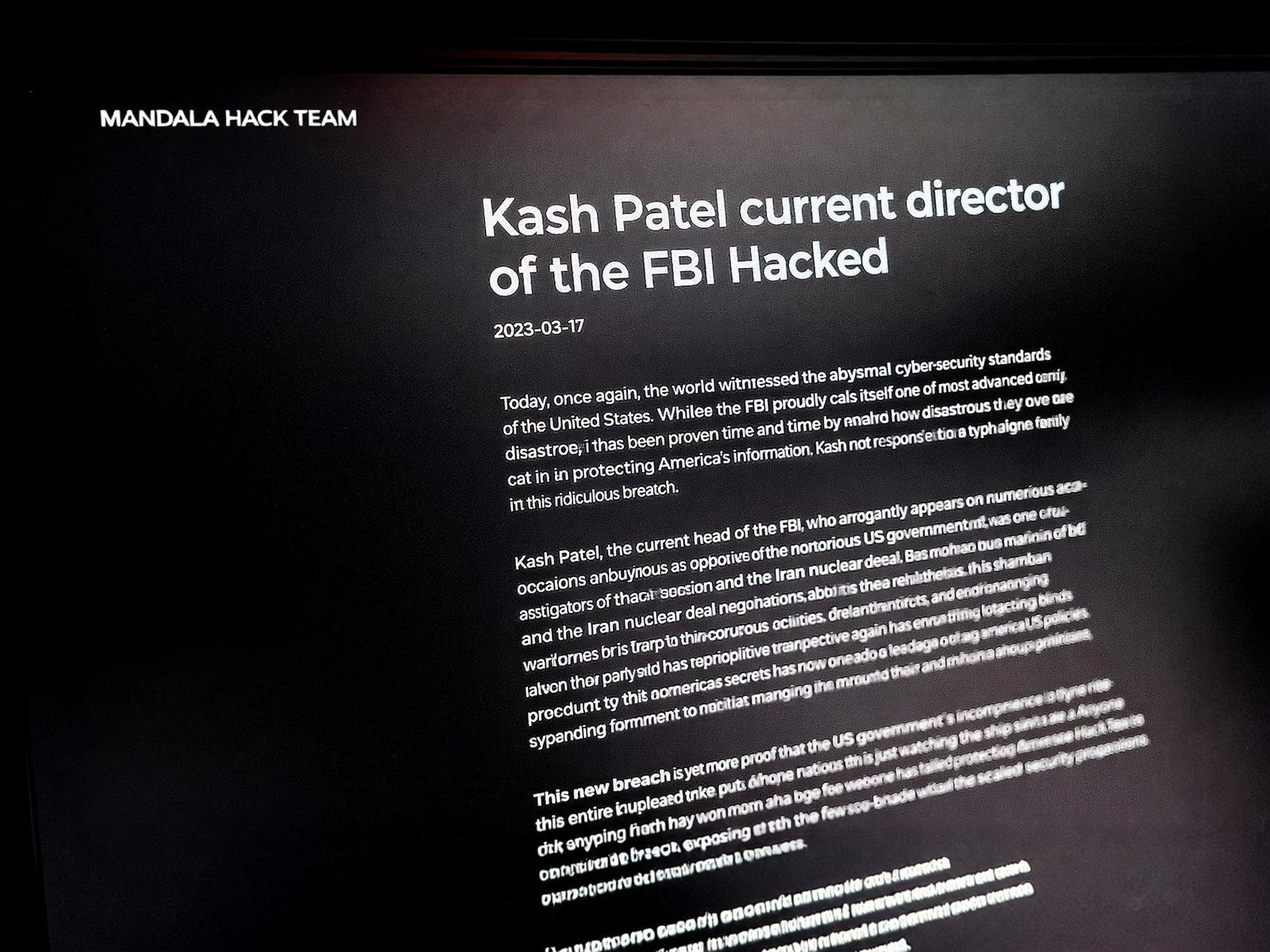
The group calling itself Handala Hack Team claimed responsibility for the breach, declaring on its website that Patel had joined its list of successfully targeted individuals. In a statement to Reuters, the FBI confirmed that Patel’s personal email had been targeted and said it had taken steps to mitigate risks associated with the intrusion.
Officials emphasized that the leaked material was “historical in nature” and did not include classified or government-sensitive information. The emails are reported to date back to 2010 and 2019.
A Network of Personas and Expanding Cyber Footprint
Cybersecurity researchers describe Handala as part of a broader ecosystem of state-linked or state-aligned cyber personas associated with Iran’s Ministry of Intelligence and Security (MOIS). The group has been tracked under multiple aliases, including Banished Kitten, Cobalt Mystique, Red Sandstorm, and Void Manticore, and has also operated under the persona Homeland Justice in campaigns targeting Albanian entities.
Another persona, Karma, previously linked to MOIS-affiliated operations, is believed by analysts to have been largely subsumed by Handala since late 2023.
According to findings by cybersecurity firm StealthMole, Handala maintains a layered online infrastructure spanning surface web domains, Tor-based services, and external hosting platforms such as MEGA. The group has also used cybercrime forums like BreachForums to publicize its activities.
FCRF Launches Premier CISO Certification Amid Rising Demand for Cybersecurity Leadership
Tactics, Targets, and the Use of Disruption
Security analysts say Handala’s operations differ from financially motivated cybercrime, focusing instead on disruption, psychological impact, and geopolitical signaling. The group has frequently targeted IT and service providers, often gaining initial access through compromised VPN credentials.
Researchers at Check Point reported identifying hundreds of login and brute-force attempts tied to infrastructure associated with the group. Once inside networks, attackers have leveraged Remote Desktop Protocol (RDP) for lateral movement and deployed wiper malware, including variants referred to as Handala Wiper and Handala PowerShell Wiper.
In some cases, attackers have used legitimate disk encryption tools like VeraCrypt to complicate recovery efforts after wiping systems.
The group has claimed responsibility for an attack on medical technology company Stryker, which it said involved deleting large volumes of data and disabling thousands of devices. Stryker stated that the incident had been contained and was confined to its internal Microsoft environment, with no evidence of further propagation.
Geopolitics, Countermeasures, and Ongoing Investigations
The activity comes amid heightened tensions linked to the broader U.S.-Israel-Iran conflict, with cybersecurity experts noting an increase in disruptive cyber operations targeting Western organizations and critical infrastructure.
U.S. authorities have taken steps to disrupt the group’s online presence, seizing several domains allegedly used in its operations, including justicehomeland[.]org and handala-hack[.]to. The U.S. Department of Justice said the domains had been used to conduct psychological operations, including publishing sensitive data and issuing threats against journalists and dissidents.
The U.S. government has also announced a reward of up to $10 million for information on individuals linked to the group.
Cybersecurity agencies, including Microsoft and the Cybersecurity and Infrastructure Security Agency (CISA), have issued guidance urging organizations to strengthen identity security, enforce phishing-resistant multi-factor authentication, and apply least-privilege access controls.
Investigators say the attackers have increasingly relied on social engineering, using platforms like Telegram as command-and-control infrastructure and disguising malware as legitimate applications such as KeePass or WhatsApp to gain persistent access.
Analysts warn that such tactics, combined with the use of legitimate administrative tools and criminal malware ecosystems, complicate attribution and detection. They also point to a growing trend of decentralized, state-linked cyber activity that blends espionage, disruption, and influence operations across global networks.