Cybersecurity researchers have identified a new malware campaign in which attackers are exploiting Microsoft Visual Studio Code (VS Code) projects as a delivery mechanism. The campaign, attributed to a North Korea-linked threat actor known as Team 8, is associated with a broader operation referred to as the “Contagious Interview” campaign.
According to findings published by NTT Security, the attackers distribute malicious repositories disguised as legitimate development projects, often with themes related to blockchain technologies. Once a user opens and trusts the repository in VS Code, a configuration file embedded within the project initiates the attack sequence.
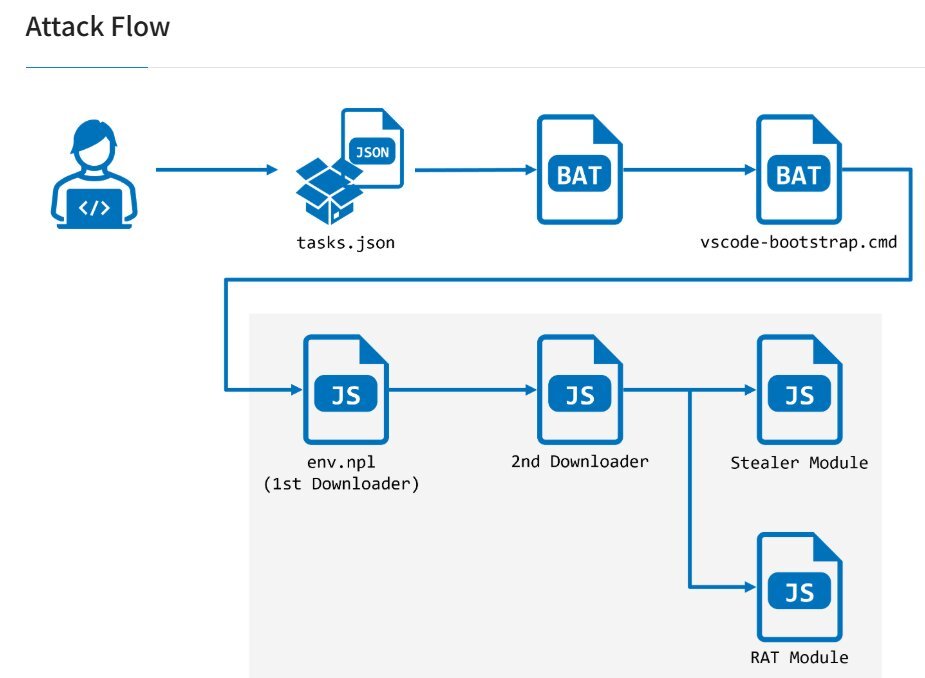
The technique leverages the “tasks.json” auto-run feature in VS Code, allowing code execution when the project folder is opened. Researchers note that this approach enables attackers to bypass traditional execution prompts, making the infection process both discreet and effective.
FCRF Launches Premier CISO Certification Amid Rising Demand for Cybersecurity Leadership
A Multi-Stage Infection Chain
The malware, named StoatWaffle, operates through a structured, multi-stage infection chain designed to maintain persistence and expand its capabilities. The initial stage involves a Node.js-based loader that connects repeatedly to a command-and-control (C2) server, executing instructions received remotely.
A second downloader module is subsequently deployed, continuing communication with the C2 infrastructure and enabling the rapid delivery of additional malicious components. This layered approach allows attackers to adapt the payload dynamically based on the compromised environment.
The malware retrieves its payloads from web-hosted infrastructure, including services such as Vercel, and executes them using system-level commands. It can also install Node.js on systems where it is not already present, ensuring compatibility across different operating environments.
Data Theft and Remote Control Capabilities
One of the core components of StoatWaffle is a stealer module designed to extract sensitive information from infected systems. The module targets browser-stored credentials, extension data, and information related to installed software.
If the victim uses Chromium-based browsers, the malware collects both stored credentials and browser extension data. In the case of Firefox, it extracts similar data sets by accessing browser-specific storage files. The malware reads configuration files such as “extensions.json” to identify installed extensions and selectively target them.
On macOS systems, the stealer extends its reach to the Keychain database, while on Windows environments, it can access system data through Windows Subsystem for Linux (WSL). The collected information is then transmitted back to the attackers’ command-and-control servers.
In addition to data exfiltration, another module functions as a remote access trojan (RAT), enabling attackers to execute commands on infected machines and retrieve outputs. Together, these capabilities allow for both comprehensive data theft and sustained remote control.
Evolving Campaign Tactics and Attribution
Researchers have linked StoatWaffle to Team 8, a threat actor previously associated with the Contagious Interview campaign. Earlier phases of the campaign reportedly relied on different malware strains, including tools such as OtterCookie, before transitioning to the newly identified variant around December 2025.
The use of developer-focused platforms and tools marks a shift in targeting strategies, reflecting a growing interest in infiltrating software development environments. By embedding malicious configurations within project files, attackers are able to exploit trust mechanisms inherent in collaborative coding workflows.