A relatively obscure hacker group with suspected links to Iran has been quietly targeting energy companies across the Middle East, stealing documents from their contractors and vendors while wildly inflating claims about the scale of the damage, according to research published by cybersecurity firm Resecurity.
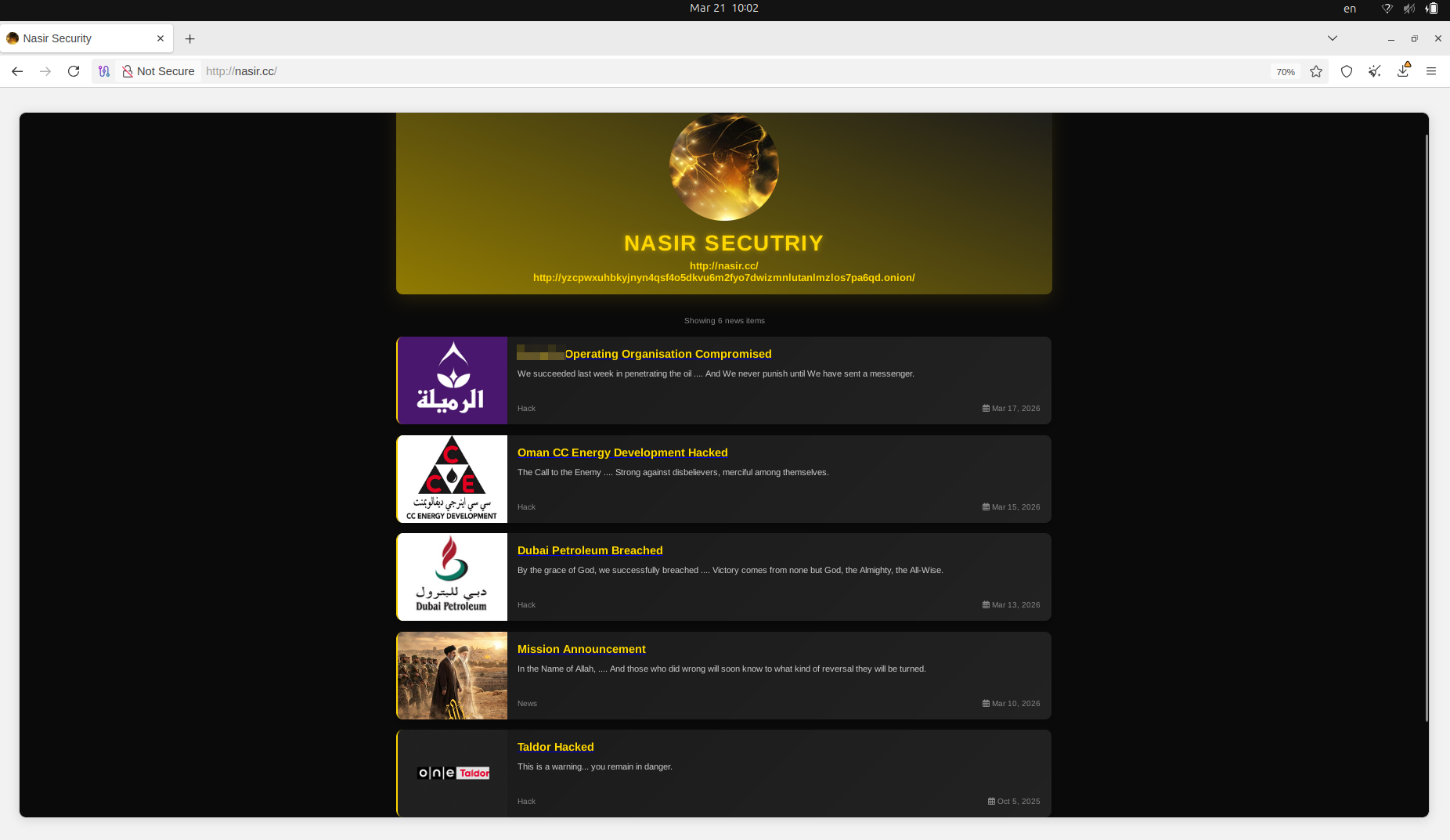
The group, calling itself Nasir Security, surfaced in October 2025 and has since gone after oil and gas organizations in the UAE, Oman, Iraq, and Saudi Arabia. But investigators say the group has not actually breached any of the major energy companies it claims as victims. Instead, it has been working its way through their supply chains, compromising smaller contractors and vendors, then presenting the stolen documents as if they had come directly from the energy giants themselves.
“The pattern across all observed claims is an overstated volume of stolen information, with a misinterpreted source for the actual leak,” Resecurity wrote in its assessment.
FCRF Launches Premier CISO Certification Amid Rising Demand for Cybersecurity Leadership
The firm estimates the group has claimed to have stolen over 827 gigabytes of data across its operations, a figure it describes as a clear exaggeration of what was actually taken from third-party vendors.
Read Full Report: Pro-Iranian Nasir Security is Targeting The Energy Sector in the Middle East
A Long Pause, Then a Flurry
After its debut attack in October 2025 against Taldor, a major Israeli IT company, Nasir Security went dark for roughly five months. That silence, researchers noted, sets it apart from typical ransomware gangs that hit targets in rapid succession for financial gain.
The group resurfaced in March 2026, publishing claims against Dubai Petroleum and CC Energy Development in Oman. On March 21, it added Al-Safi Oil Company, a Saudi Arabian fuel retailer operating under the name PURE IN, to its list. Resecurity said that in that particular case, the data had actually been lifted from a fire alarm and safety equipment vendor, not the oil company itself.
None of the affected organizations were contacted or extorted, according to Resecurity, which spoke directly with some of them. That detail points to ideological motivation rather than financial gain.
Who Is Behind It?
The group’s identity is a tangled web of shifting names and murky affiliations. It launched as “Sons of Hezbollah Lebanon,” later rebranded as “Sons of Al-Nusayr,” and most recently called itself “Al-Nasir Resistance.”
Resecurity believes the group is likely made up of hired operatives or individuals acting on behalf of Iran or affiliated proxies rather than being a formal state-sponsored unit. Some members may be from outside the region but hold pro-Iranian views. The deliberate misspelling of affiliated group names, investigators noted, appears designed to create an impression of legitimacy while muddying any formal link to those organizations.
Attribution, the firm cautioned, should be treated carefully. Nasir Security has no social media presence, maintained a low profile for most of its existence, and operates during a period when Iran and its proxies are known to be running disinformation and influence campaigns at scale. The risk of false flags and psychological operations is high.
The Real Danger in the Documents
Even if the breaches are far smaller than advertised, Resecurity is not dismissing the threat. The documents that were stolen, which include engineering schematics, contracts, and risk assessments, could give adversaries a road map for planning physical attacks on energy infrastructure.
“Documents acquired by Iranian threat actors may provide them with additional context and insights to plan further attacks,” the firm wrote, including identifying which parts of a facility, if damaged, would be hardest to repair and most disruptive to operations.
That concern is particularly relevant given the broader context. Iranian forces have used drones and missiles to strike energy infrastructure across the Gulf Cooperation Council, and the Strait of Hormuz has faced repeated threats of closure. Cyber operations, the firm argues, are being used to amplify and support those kinetic efforts rather than replace them.
How They Operate
The group uses a combination of phishing emails, impersonation, and attacks on publicly accessible applications to gain entry into contractor systems. Data is then pulled from poorly secured cloud storage. Their data leak site, registered through Namecheap, has both a public web address and a mirror on the Tor network.
Typically, the group releases a handful of sample documents, between eight and ten files, without posting the full trove. That tactic keeps their victims and observers in a state of uncertainty while avoiding the exposure that would come with a full dump.
What Companies Should Do
Resecurity is recommending that energy sector companies and their partners accelerate third-party risk assessments and tighten monitoring of vendors and contractors. The supply chain, the firm argues, is now a primary attack vector for Iranian threat actors looking to rack up visible wins without necessarily causing the kind of damage that would demand a direct military or diplomatic response.
The group’s data leak site can be found at NASIR.CC on the open web, with a corresponding Tor mirror for those operating in the dark web ecosystem.



