On a winter morning late last December, as temperatures dropped across Poland, cyber intruders quietly moved through the digital nervous system of the country’s energy infrastructure. Their actions were calculated, destructive and unusually brazen — yet the lights stayed on.
A Coordinated Strike in Midwinter
On December 29, 2025, Poland faced a coordinated series of cyberattacks that targeted more than 30 wind and solar farms, a manufacturing company, and a large combined heat and power plant supplying electricity and heat to nearly half a million people. The incidents unfolded during a period of severe winter weather, a moment when energy systems are under peak strain.
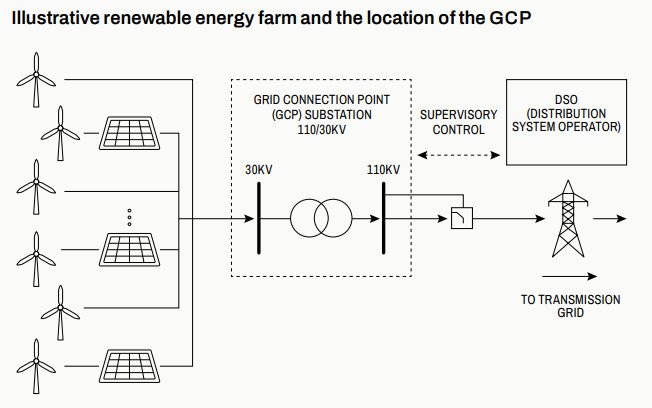
According to a detailed report published by CERT Polska, the attackers sought to cause disruption through sabotage rather than extortion. Communications with grid operators were disrupted, and remote management capabilities were blocked, but electricity generation and heat supply continued without interruption.
The attacks marked a rare convergence of damage to both traditional IT systems and operational technology — the industrial control equipment that governs physical processes. CERT Polska said it released the findings to raise awareness of what it described as a growing risk of cyber sabotage against critical infrastructure.
Certified Cyber Crime Investigator Course Launched by Centre for Police Technology
Inside the Network: Access, Movement and Control
Investigators found that the attackers gained initial access through exposed FortiGate devices used for VPN and firewall functions, often lacking multi-factor authentication. Some systems were affected by known vulnerabilities, while reused credentials allowed the intruders to move laterally between sites.
Once administrative access was obtained, the attackers mapped internal networks over a prolonged period. They reset devices to erase evidence and slow recovery efforts, then launched automated destructive actions in sequence. Firmware was corrupted on Hitachi remote terminal units, Mikronika controllers were wiped, protection relays were disabled, and Moxa serial devices were sabotaged.
Human-machine interface computers — a key link between operators and industrial systems — were compromised using custom wiper malware. These actions severed communications and remote control capabilities but stopped short of interrupting electricity production.
Wiper Malware Without a Ransom
The attacks relied on previously unknown wiper malware designed solely to destroy data. Investigators identified two tools: a Windows-based wiper known as DynoWiper and a PowerShell script dubbed LazyWiper.
DynoWiper corrupted and deleted files across disks by overwriting them with random data, rendering recovery impossible. Researchers noted that the tool lacked command-and-control infrastructure, persistence mechanisms, or attempts at concealment. LazyWiper, by contrast, targeted a wide range of file types and partially overwrote them to make systems unusable. Analysts believe portions of the script may have been generated using an artificial intelligence tool.
The malware was distributed across networks using malicious Group Policy tasks within Active Directory environments, allowing rapid propagation once control was established.
In one case involving a large combined heat and power plant, attackers spent months inside the network stealing sensitive data and escalating privileges. When they attempted to activate the wiper malware, the plant’s endpoint detection and response system stopped the attack. On the same day, a manufacturing company was also hit in what investigators described as an opportunistic strike using the same tools.
Attribution and a First of Its Kind
CERT Polska attributed the campaign to a threat cluster known as Static Tundra, which it linked to Russia’s FSB Center 16. The assessment was based on analysis of attack infrastructure, including compromised virtual private servers, Cisco routers, traffic patterns and the characteristics of anonymizing services.
The infrastructure showed a high degree of overlap with activity previously described under different names by major cybersecurity firms — including “Berserk Bear,” “Ghost Blizzard,” and “Dragonfly” — all associated with long-standing interest in the energy sector and the capability to attack industrial devices.
While the wiper malware shared some similarities with tools used by Sandworm, another Russia-linked group, CERT Polska said the overlap was insufficient for firm attribution. Other security firms, including ESET and Dragos, have suggested with moderate confidence that Sandworm may have been involved.
What sets this incident apart, CERT Polska noted, is that it represents the first publicly documented destructive operation attributed to the Static Tundra activity cluster — an escalation that underscores how cyber operations against energy infrastructure are evolving from espionage toward overt sabotage, even when the immediate physical impact is contained.