A ransomware group known for selling stolen data rather than locking files says it has taken hundreds of gigabytes of sensitive information from McDonald’s operations in India, a claim that has sharpened concerns about customer privacy and corporate cybersecurity across the region.
A Claim Emerges on the Dark Web
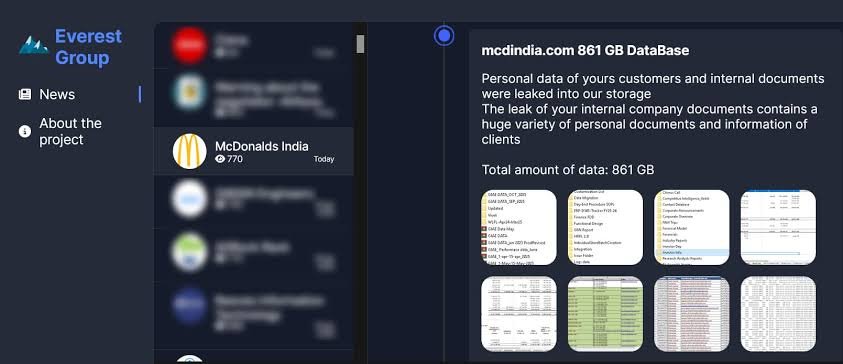
On January 20, 2026, a post appeared on a dark web leak site operated by the Everest ransomware group. The message was blunt. The attackers said they had exfiltrated 861 gigabytes of data from McDonald’s India, describing a trove that included internal company records and what they called a “huge variety of personal documents and information of clients.”
The group warned that the data would be made public if the company failed to respond within a set deadline. Such postings, increasingly common in major cyberextortion cases, are designed to apply pressure not through service disruption but through the threat of exposure. In this case, the attackers asserted that personal data of customers, along with internal documents, had already been transferred to their storage systems.
McDonald’s India has not publicly confirmed that a breach occurred. The absence of official verification has left customers, regulators, and cybersecurity analysts relying largely on the attackers’ statements to understand the scope and nature of the alleged intrusion.
Certified Cyber Crime Investigator Course Launched by Centre for Police Technology
The Risks Inside Stolen Records
According to the attackers’ claims, the stolen material includes internal records that could pose significant risks if released. Such data, security experts note, is often valuable not only for its immediate sensitivity but also for how it can be combined with other information.
Identity theft and targeted phishing campaigns are among the most common downstream threats following large-scale data exfiltration. Internal documents can provide insight into company processes, vendor relationships, and employee structures, while personal customer information can be used to craft convincing scams aimed at individuals or organizations across a region
The attackers framed the breach as comprehensive, suggesting that both corporate and personal data were compromised. While those claims have not been independently verified, the volume cited—hundreds of gigabytes—places the incident among the larger alleged data thefts reported in recent months.
A Ransomware Group’s Playbook
Everest is a Russian-speaking ransomware operation that first emerged in December 2020. In its early stages, the group focused primarily on data exfiltration, stealing information and using it as leverage rather than immediately encrypting victims’ systems. By early 2021, it had expanded to full ransomware capabilities, using dual AES and DES encryption while continuing to emphasize data theft.
The group is particularly known for what cybersecurity firms describe as “pure extortion” tactics. Instead of relying solely on operational disruption, Everest specializes in stealing and selling sensitive corporate data, or threatening to publish it outright. This approach has made its leak site a central element of its operations.
In recent years, Everest has claimed responsibility for several high-profile incidents, including an alleged theft of 900 gigabytes of data from Nissan Motor Corporation in January 2026 and a breach at Dublin Airport in October 2025 that reportedly compromised 1.5 million passenger records. Those cases, like the current claim involving McDonald’s India, relied heavily on public pressure created through online disclosures.
McDonald’s India and an Unanswered Question
McDonald’s presence in India is structured through two separate business entities. Connaught Plaza Restaurants oversees operations in North and East India, while Hardcastle Restaurants manages outlets in the West and South. Together, they have served millions of customers since the brand entered the country in 1996.
As of now, neither entity has confirmed details of the alleged cyberattack. Without such confirmation, it remains unclear which systems were affected, how access may have been gained, or whether customer data was indeed exposed at the scale described by the attackers.