A major leak tied to BreachForums, one of the most persistent cybercrime forums on the dark web, has spilled details linked to roughly 324,000 user accounts. Resecurity, a cyber threat intelligence firm, said the leaked MySQL database contains metadata for 323,986 users and has made the dataset available for download for independent analysis, while warning researchers not to fetch it from untrusted sources due to malware risk.
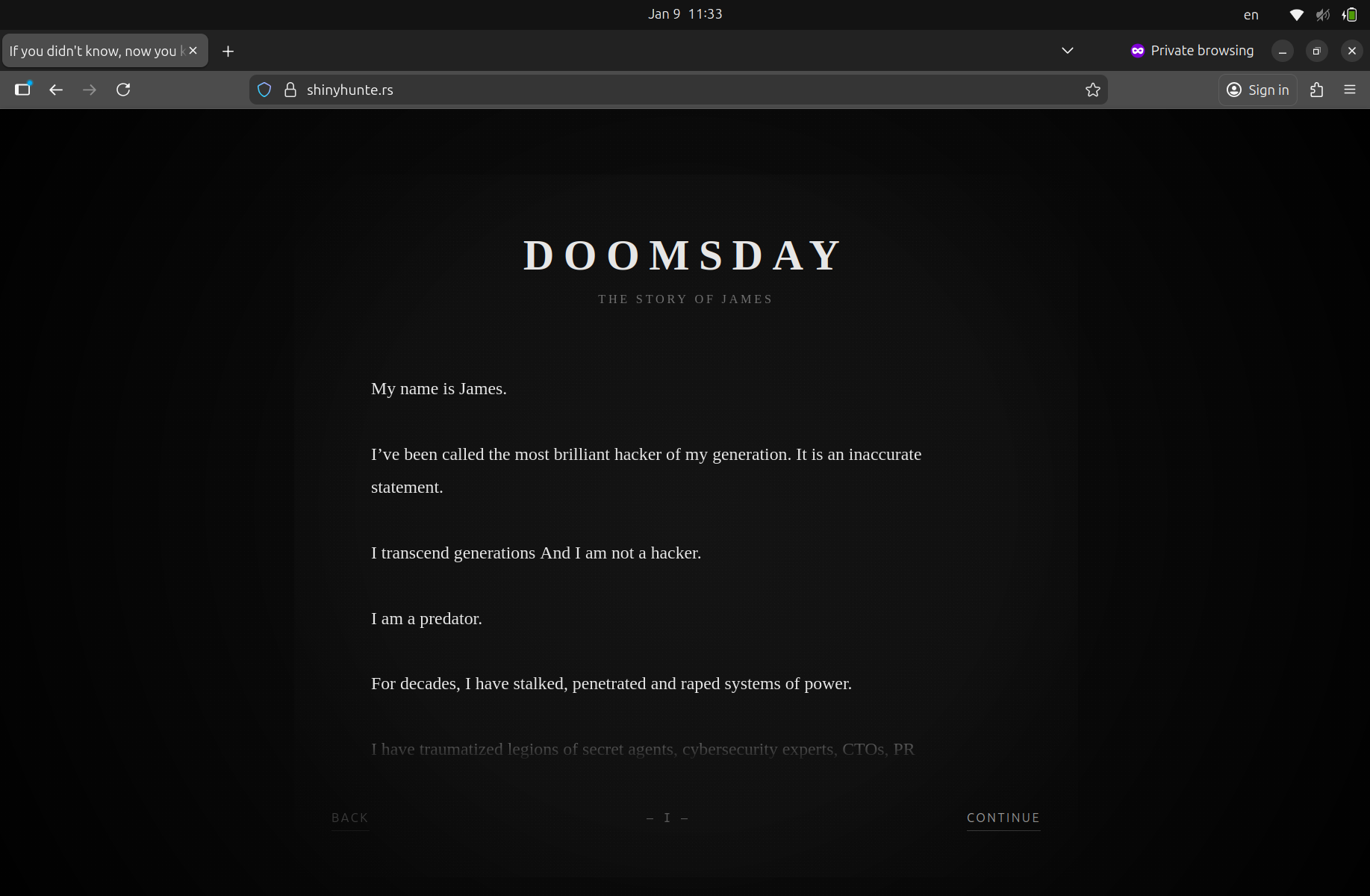
The stolen data later appeared on shinyhunte[.]rs, alongside a manifesto posted by a self-styled cyber outlaw calling himself “James.” Resecurity said the release is likely to increase real-world exposure for actors who relied on the forum’s perceived anonymity.
Certified Cyber Crime Investigator Course Launched by Centre for Police Technology
What Resecurity Says Was Leaked
Resecurity said the leaked dataset was extracted from a MySQL table linked to a MyBB-based forum deployment. The dump includes account-level metadata that can be used to profile and cross-reference users.
Resecurity said the exposed records include:
- Email addresses and usernames
- Argon2-hashed passwords
- Forum metadata tied to public posts, private messages, and other account records
- PGP keys tied to certain accounts and handles
The cybersecurity firm also said some entries appear edited or partially scrubbed, including the use of placeholder IP values such as 127.0.0.9, which researchers view as an operational security tactic to muddy attribution.
Have I Been Pwned Tracks the Incident
Have I Been Pwned, the breach notification platform, listed the BreachForums incident as an August 2025 breach and added it to its database on January 10, 2026. The listing indicates the leak includes about 324,000 unique email addresses along with usernames and Argon2-hashed passwords.
Resecurity’s review aligns with that timeline, and Resecurity flagged an additional detail that caught analysts’ attention: the most recent registration date inside the leaked user table is August 11, 2025, the same day the prior BreachForums presence at breachforums[.]hn went offline. Resecurity said this timing suggests the data may have been taken as the forum was entering its final hours.
Why Resecurity Links This Leak to Forum “Recovery” Failures
Resecurity said the database could have been acquired through a web application vulnerability or a misconfiguration. BreachForums’ current administrator, using the alias N/A, publicly addressed the incident and claimed the exposed table originated from an older leak during an August 2025 restoration effort.
In that statement, the administrator said the users table and a forum PGP key were temporarily stored in an unsecured folder during recovery and that the folder was downloaded once during that window. Resecurity noted the statement, while emphasizing that independent verification of internal claims remains difficult.
Who Appears in the Data, According to Resecurity
Resecurity said the leaked records include accounts tied to real individuals active in cybercrime circles, including actors previously linked to groups such as GnosticPlayers. Resecurity also said PGP keys tied to accounts using handles such as ShinyHunters and IntelBroker were found in the dump.
Resecurity cautioned that parts of the dataset show signs of tampering, but said a substantial portion appears authentic and can be cross-checked against other sources tied to known actors.
Resecurity Flags Global Activity, Including MENA Signals
Resecurity said it analyzed registration and “last seen” IP data contained in the dump, while warning that VPNs and proxies limit confidence. Even so, Resecurity said the records indicate significant usage across the United States and Europe, with additional signals from the Middle East and North Africa.
Resecurity’s country-level indicators included:
- United States
- Germany, the Netherlands, France, the United Kingdom
- Turkey
- Morocco, Jordan, Egypt
Resecurity also said some usernames and email patterns suggested linguistic origins, including French, Arabic, Turkish, Russian, and Chinese spellings. Resecurity described this as consistent with a broad, international user base that used both anonymous email services and mainstream providers such as Gmail.
The shinyhunte[.]rs Posting and Resecurity’s Safety Warning
Resecurity said the allegedly stolen database was posted to shinyhunte[.]rs and that the same resource has appeared through Tor mirrors. Resecurity warned researchers not to download the dump from unofficial locations, citing the risk of embedded malicious code and poisoned archives.
Resecurity described the incident as an example of a cybercrime ecosystem failing on basic security controls. Resecurity’s position is that breaches can hit criminal infrastructure just as they hit legitimate businesses, and that exposure of actor metadata can disrupt illicit operations.
The “James” Manifesto and Resecurity’s Disinformation Concern
The dump was posted alongside a lengthy manifesto signed “James,” written in a theatrical tone and spread across multiple fragments. Resecurity published the full text in its research and framed it as part intimidation, part attention-seeking, and part narrative-building.
Resecurity also pointed to a recurring issue: underground actors often push misleading storylines to confuse attribution, shift blame, or bait investigators and media into repeating false trails. Resecurity said readers should not treat the manifesto’s identity claims as verified.
BreachForums’ Repeated Resurrections
Resecurity placed the leak in the context of BreachForums’ history as a successor to RaidForums, which law enforcement seized in February 2022.
Key milestones frequently cited by Resecurity and other trackers include:
- BreachForums v1 operated from March 2022 to March 2023 under the alias pompompurin
- Authorities arrested Conor Brian Fitzpatrick in 2023, and the forum later returned under new management linked to ShinyHunters-aligned actors and administrators such as Baphomet
- The forum faced takedowns and domain seizures in 2024, then reappeared using alternate domains, hosting changes, and Tor mirrors
- The latest .bf incarnation remains active, with infrastructure indicators showing ongoing reliance on DDoS-Guard name servers in some configurations
Resecurity has repeatedly documented how these forums survive by cycling domains, shifting hosting providers, and leaning on protection services that accept high-risk clients.
Where Resecurity Places “ShinyHunters” in the Wider Ecosystem
Resecurity drew a distinction between brand names and real actor sets, arguing that “ShinyHunters” has been reused, rebranded, and repurposed by different clusters over time. Resecurity said rebranding is routine in underground ecosystems and can confuse observers who treat a name as a stable identity.
Resecurity also tied the broader phenomenon to “The Com,” described as a loosely organized, youth-heavy cybercriminal ecosystem where members move between Telegram channels, chat groups, and short-lived collectives. Resecurity has used “ShinyHunters” in research as a collaborative alias to illustrate how young actors get pulled into account takeovers, SIM swapping, crypto theft, swotting, and sextortion.
Why Resecurity Says the Leak Raises Real-World Risk
Resecurity warned that publishing this dataset changes the threat landscape for those named inside it. Even if the underlying breach occurred months earlier, public release enables rapid cross-referencing with:
- Previous breach corpuses
- OSINT and social media traces
- PGP fingerprints and reused handles
- Email reuse across services
Resecurity said the result is a higher likelihood that actors will face identification, disruption, and arrests. Resecurity also warned the leak may trigger retaliation inside cybercrime circles, where exposure can be treated as betrayal.
A core point in Resecurity’s assessment is that information that once sat inside a semi-private forum can now be indexed, searched, and correlated at scale.
Victim Reporting Resources Referenced in Resecurity’s Material
Resecurity also highlighted reporting resources for victims harmed by tactics linked to these ecosystems, including sextortion and exploitation.
Commonly cited resources include:
- FBI Internet Crime Complaint Center (IC3)
- FBI field office contact channels
- National Center for Missing and Exploited Children (NCMEC) and its Take It Down service
What Happens Next
Resecurity’s view is that the BreachForums leak will have second-order impacts beyond embarrassment. If defenders and investigators can validate identities, the dataset can support disruption efforts, help map relationships, and expose infrastructure patterns.
Resecurity also expects counter-moves. Underground operators have a long track record of:
- Rebranding after exposure
- Moving to new forums and invite-only channels
- Scrubbing records, rotating keys, and resetting infrastructure
The immediate question is not whether BreachForums will attempt another return. It is how many of its users will decide the risk is no longer worth it after Resecurity’s publication put the forum’s internal records into the open.
About the author – Ayesha Aayat is a law student and contributor covering cybercrime, online frauds, and digital safety concerns. Her writing aims to raise awareness about evolving cyber threats and legal responses.


