A newly advertised malware service promises to steal vast amounts of personal data while remaining invisible to traditional defenses. But early analysis suggests that, behind the marketing bravado, the operation reflects both the evolution—and the enduring weaknesses—of the cybercrime economy.
A New Stealer, Marketed as Invisible
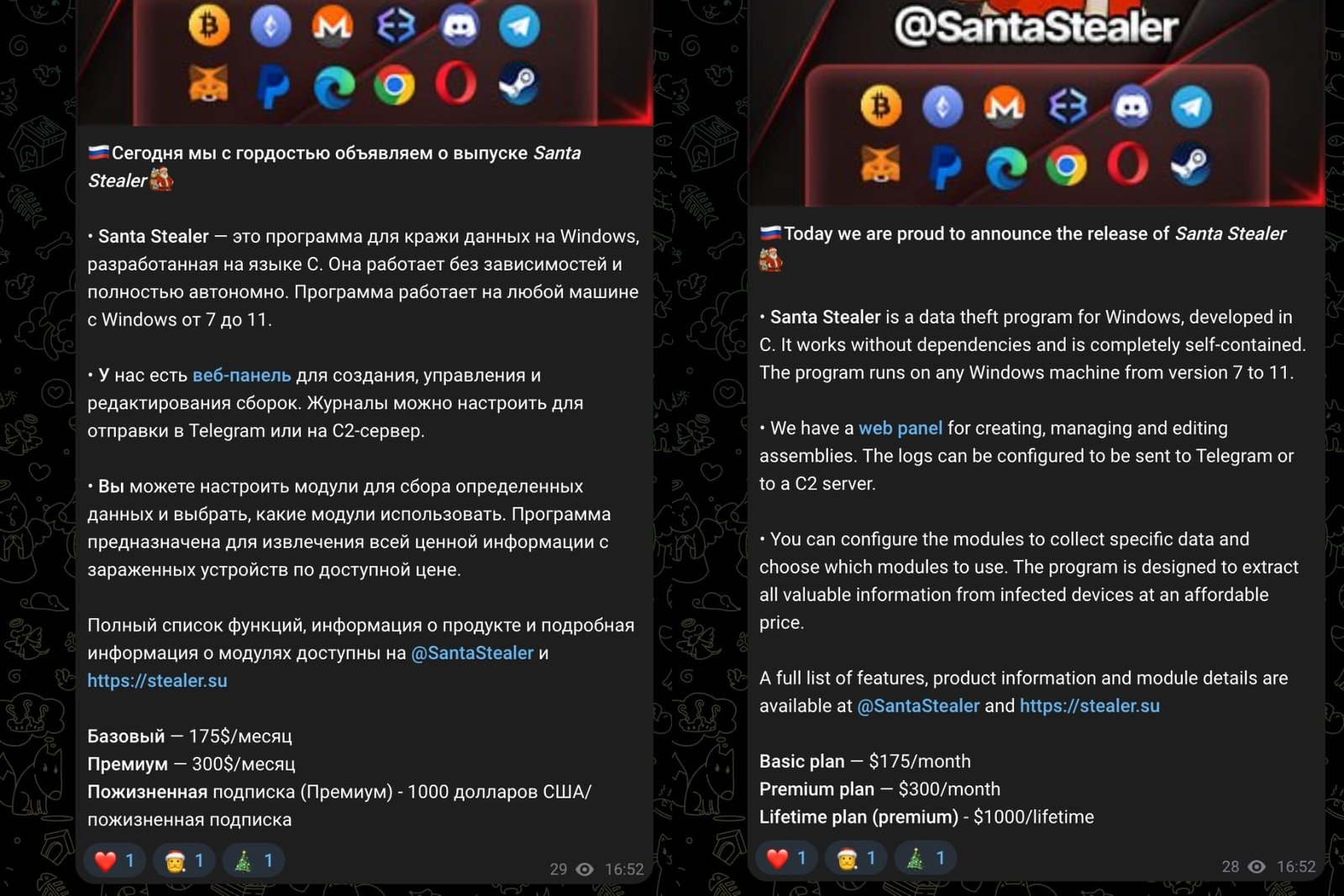
In recent weeks, a malware-as-a-service operation calling itself SantaStealer has surfaced on Telegram channels and underground hacker forums, promoted as a next-generation information stealer capable of operating entirely in memory to evade file-based detection. The pitch is familiar to anyone who tracks cybercrime markets: stealth, modular design, and a promise of resilience against modern security protections.
Security researchers at Rapid7, who analyzed several samples and gained access to the service’s affiliate panel, describe SantaStealer as an ambitious but uneven entrant into a crowded ecosystem of credential-harvesting malware. According to their findings, the operation appears to be a rebranding of an earlier project known as BluelineStealer, now being prepared for a wider launch before the end of the year.
The developer, believed to be Russian-speaking, is marketing the tool through subscription tiers—$175 a month for a basic version and $300 for a premium offering—placing SantaStealer squarely within the established commercial norms of cybercrime-as-a-service.
How the Malware Is Designed to Work
At a technical level, SantaStealer reflects the modular engineering that has become standard among modern info-stealers. Rapid7 researchers found that it uses 14 distinct data-collection modules, each running in its own thread. Stolen data is first written to memory, then compressed into ZIP archives and exfiltrated in 10-megabyte chunks to a hardcoded command-and-control server over port 6767.
The scope of data targeted is broad. The modules are designed to harvest browser-stored information such as passwords, cookies, browsing history, and saved credit card details, alongside data from applications including Telegram, Discord, and Steam. Cryptocurrency wallet applications and browser extensions are also in scope, as are documents stored on the victim’s system. The malware can additionally capture screenshots of the user’s desktop, expanding its utility for account takeover and fraud.
One notable feature is an embedded executable intended to bypass Chrome’s App-Bound Encryption, a security mechanism introduced in July 2024 to protect sensitive browser data. While SantaStealer advertises this capability as a differentiator, Rapid7 notes that similar bypass techniques have already been adopted by multiple active information stealers.
Distribution, Deception, and Operational Tradecraft
Although SantaStealer is not yet being distributed at scale, researchers say its likely infection vectors mirror those of other commodity stealers. Cybercriminals increasingly favor ClickFix-style attacks, which rely on social engineering rather than exploits—tricking users into pasting malicious commands into the Windows terminal under the guise of fixing a technical problem.
More traditional methods remain common: phishing emails with malicious attachments, trojanized pirated software, torrent downloads, malvertising campaigns, and deceptive comments on platforms like YouTube that lure users toward infected files.
Configuration options within SantaStealer allow operators to exclude systems in the Commonwealth of Independent States, a longstanding convention in parts of the cybercrime world, and to delay execution to create periods of inactivity that may mislead victims or analysts.
Hype, Gaps, and What the Early Evidence Shows
Despite its marketing claims, Rapid7’s assessment suggests that SantaStealer has not yet achieved the level of sophistication implied by its advertising. The samples analyzed were described as “far from undetectable” and not especially difficult to reverse engineer. In some cases, leaked builds included unencrypted strings and intact symbol names—mistakes that security researchers say undermine claims of strong anti-analysis or anti-antivirus capabilities.
Such errors, Rapid7 noted, may indicate that the malware is still under development, with unfinished defensive features planned for later releases. But they also point to a recurring pattern in the cybercrime economy: rapid monetization often outpaces operational discipline.
Rapid7 advises users to be cautious with unsolicited links and attachments and to avoid running unverified code from public repositories, a reminder that even the most technically elaborate threats still depend on trust being misplaced.