The notorious XWorm malware, a “Swiss Army knife” in the world of cybercrime, has roared back to life after its original developer abandoned the project. This remote access trojan (RAT), which first appeared in 2022, has undergone a major transformation. After the original programmer stepped away, new threat actors quickly seized upon the popular tool. Now, in its latest iterations (versions 6.0, 6.4, and 6.5), the malware is spreading globally with a renewed, sophisticated architecture. It is no longer just a spy tool used to steal passwords and financial data; it has become an end-to-end extortion machine.
A Tool for Extortion: Ransomware Capabilities Emerge
The most alarming upgrade is the inclusion of a dedicated ransomware module, known as Ransomware.dll. This plugin gives the malware operator the ability to digitally lock a victim’s files and demand a ransom, typically in cryptocurrency. The encryption process is designed to target critical personal data, focusing on files within a user’s profile folders and the Documents location while cleverly avoiding system files to keep the computer running enough for the victim to pay. Once locked, the original files are deleted, and the encrypted version is given an .ENC extension. Researchers have noted a concerning code similarity between XWorm’s new module and the existing NoCry ransomware, suggesting criminals are reusing or sharing powerful encryption components.
A Swiss Army Knife of Digital Crime
Beyond file encryption, XWorm’s strength lies in its modularity—the ability to add or remove various functions through plugins. The malware now supports more than 35 unique modules that allow criminals to conduct a wide range of attacks. These modules facilitate massive data theft from multiple sources, including login details from over 35 types of web browsers, email clients, messaging apps, and crypto wallets. Other powerful plugins give the attacker remote desktop access and the ability to execute system commands silently. There is even a Webcam.dll module that can be used to monitor the victim, a chilling verification tool for the criminals to see if the infected machine is a real user’s device.
FCRF Launches CCLP Program to Train India’s Next Generation of Cyber Law Practitioners
New Channels of Attack Spread the Threat
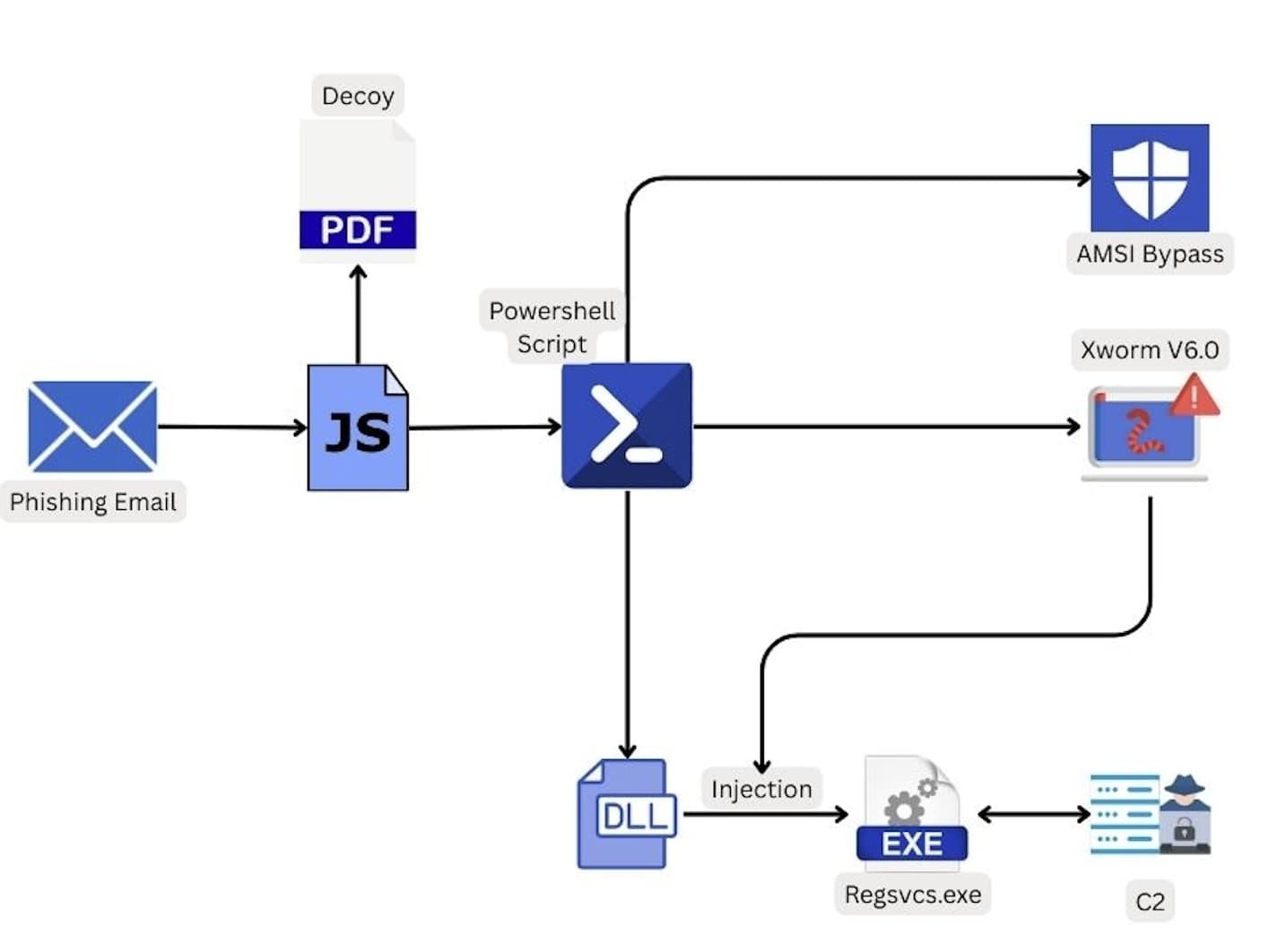
The criminals deploying XWorm are utilizing a variety of sophisticated methods to bypass defenses and infect targets. While common vectors like malicious email attachments and .LNK files are still in use, the infection chain has become more complex. One campaign uses a malicious JavaScript to kick off a complex PowerShell script, which is designed to fly under the radar of antivirus software. To fool victims, the malware is often disguised with legitimate-looking filenames, sometimes appearing as harmless applications like Discord. In other observed attacks, criminals have leveraged timely lures, such as AI-themed content, or even embedded shellcode within Microsoft Excel files (.XLAM) to ensure the malware is deployed once the file is opened.
Fixing a Flaw, Selling an Empire
XWorm’s revival began after its original developer, known as “XCoder,” disappeared from online forums. Multiple cybercriminals soon began distributing cracked or modified versions. The new, professional-grade variants are being actively marketed on hacker forums, with one account offering “lifetime access” for a ₹45,000( about $500) subscription. This professionalization suggests that the malware has moved from a single author’s project to a service model for multiple criminal groups. Importantly, the new versions have fixed a significant vulnerability—a remote code execution flaw in the old XWorm 5.6—making the tool more stable and effective for its new owners. Experts recommend that organizations adopt a multi-layered defense strategy, using tools that detect suspicious behavior rather than just looking for known file signatures, to counter this highly adaptable threat.