Cybersecurity experts have sounded the alarm after a report revealed that ten thousand WordPress websites were compromised and used to distribute sophisticated “infostealing” malware to visitors using both Windows and macOS devices. The attackers exploited older versions of the WordPress platform and outdated plugins, deploying malicious code that tricked users into downloading malware like Atomic (AKA AMOS) and SocGholish by presenting a fake browser update prompt. The malicious software is capable of stealing passwords, session cookies, cryptocurrency wallet information, and other sensitive files.
The Scope of the Compromise
A troubling new report from cybersecurity researchers at c/side details a massive digital compromise, identifying ten thousand WordPress websites that have been weaponized to deliver malicious software. This campaign targets a broad audience, impacting users running both Windows and macOS devices. The core payload is “infostealing” malware, designed to covertly exfiltrate sensitive personal and financial data.
Attack Vector and Deceptive Tactics
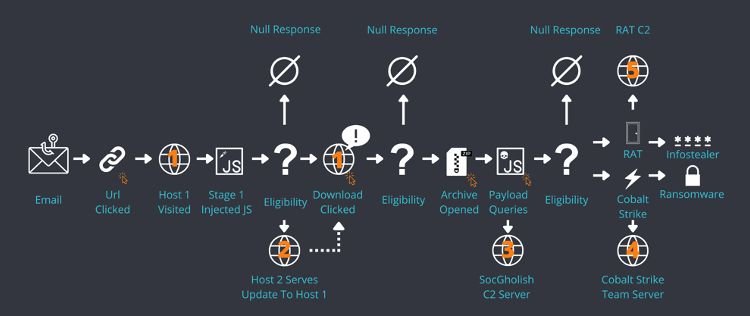
The threat actor successfully breached numerous WordPress sites, primarily by exploiting vulnerabilities in an older version of the platform (6.7.1) and an outdated plugin. Once control was established, the attackers injected malicious JavaScript code into the compromised sites. When a victim visited one of the infected pages, this code generated a fake page within an iframe, which then overlaid the legitimate content. The victim was presented with a deceptive message stating they needed to update their browser to view the site’s contents. Crucially, instead of downloading a legitimate patch, the victims were served the infostealing malware: Atomic (AKA AMOS) for macOS users, and SocGholish (a similar tool) for Windows users.
FCRF Launches CCLP Program to Train India’s Next Generation of Cyber Law Practitioners
The Threat to User Data
The malware delivered through this scheme poses a greater risk to the victims’ digital lives. These infostealers are designed to grab a wide array of sensitive information from the victim’s device, or “target endpoint.” This includes, but is not limited to:
- Passwords stored in the browser.
- Session cookies, which can be used to hijack active user sessions on other websites.
- Cryptocurrency wallet information.
- Other potentially sensitive files.
The quiet efficiency of these tools means users may be unaware their data has been compromised until it’s too late.
A Call to Action for Web Administrators
Defending against this pervasive threat hinges on proactive maintenance and security hygiene by web administrators. The researchers at c/side offer clear, critical steps for WordPress site owners:
- Platform Upgrade: The WordPress website builder platform must be immediately upgraded to version 6.7 (or newer), which was released in mid-November 2024.
- Plugin and Theme Audit: Administrators should review all installed themes and plugins, removing any that are unused. The remaining active components must be updated to their latest versions.
- Malicious Code Cleanup: Admins must diligently search for and delete any malicious scripts. Threat actors often leave a backdoor to ensure they can easily regain access, necessitating a thorough scrub.
- Log Review: Any site showing traces of compromise should have its logs reviewed for the last 90 days to fully identify the extent and type of malicious activity performed.